
A new wave of sextortion scam emails is targeting victims in multiple languages and locations around the world to blackmail victims into paying thousands of pounds in Bitcoin.
Sextortion, a scam in which a criminal threatens to share compromising sexual content of an individual unless they pay a ransom, is not a new crime but has become more common with the rise of picture sharing and the proliferation of webcam devices.
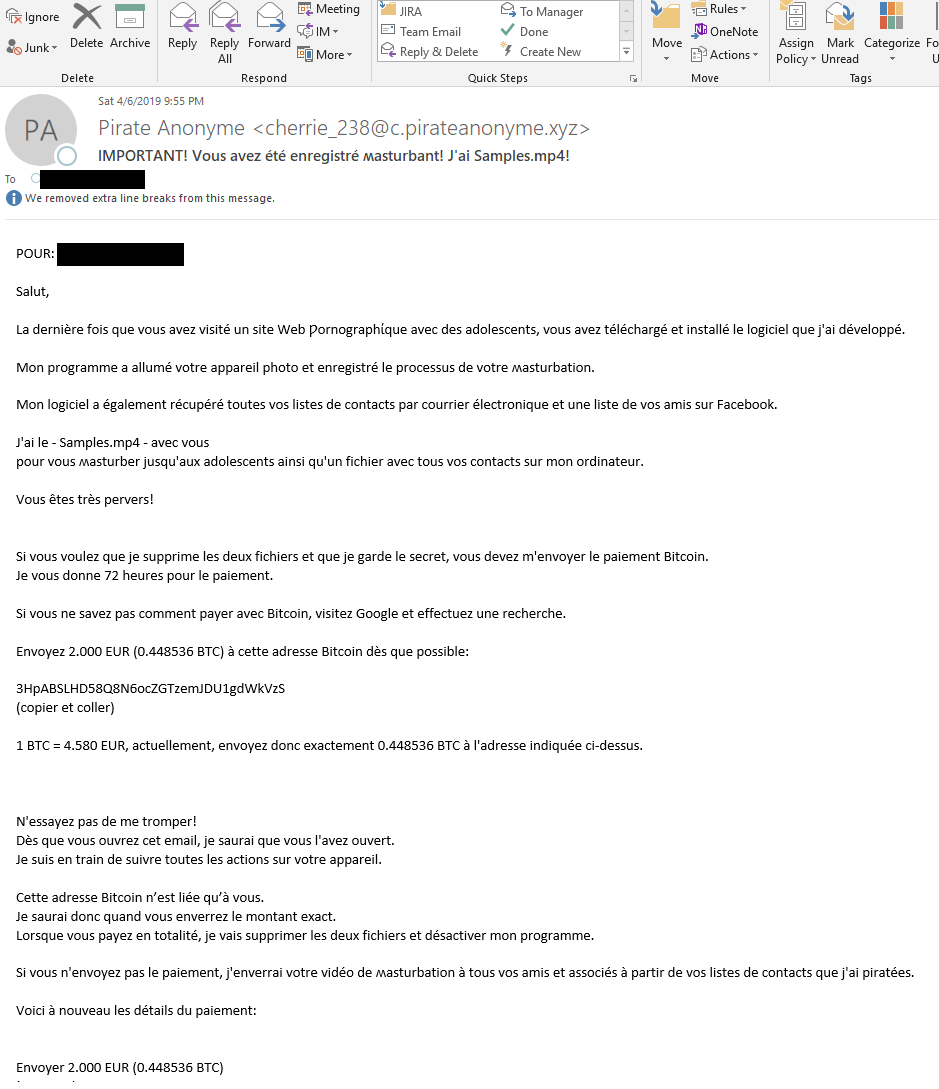
Slovakia-headquartered cybersecurity firm ESET has warned of a new sextortion email campaign that attempts to elicit around £2,000 in Bitcoin from victims. The latest wave is targeting people in Australia, the US, UK, Germany, France, Spain, Czech Republic and Russia – tailoring the scam email to the victim’s native language.
ESET says that the scammer’s Bitcoin wallet shows some have fallen for the sextortion scam.
In this particular scam, the attacker sends an email to a victim claiming to have hacked their device and captured compromising footage of the person while they watch pornography.
“The last time you visited a porn website with teenagers, you downloaded and installed the virus I developed,” the message begins.
How well do you really know your competitors?
Access the most comprehensive Company Profiles on the market, powered by GlobalData. Save hours of research. Gain competitive edge.

Thank you!
Your download email will arrive shortly
Not ready to buy yet? Download a free sample
We are confident about the unique quality of our Company Profiles. However, we want you to make the most beneficial decision for your business, so we offer a free sample that you can download by submitting the below form
By GlobalData“My program has turned on your cam and recorded the act of masturbation..”
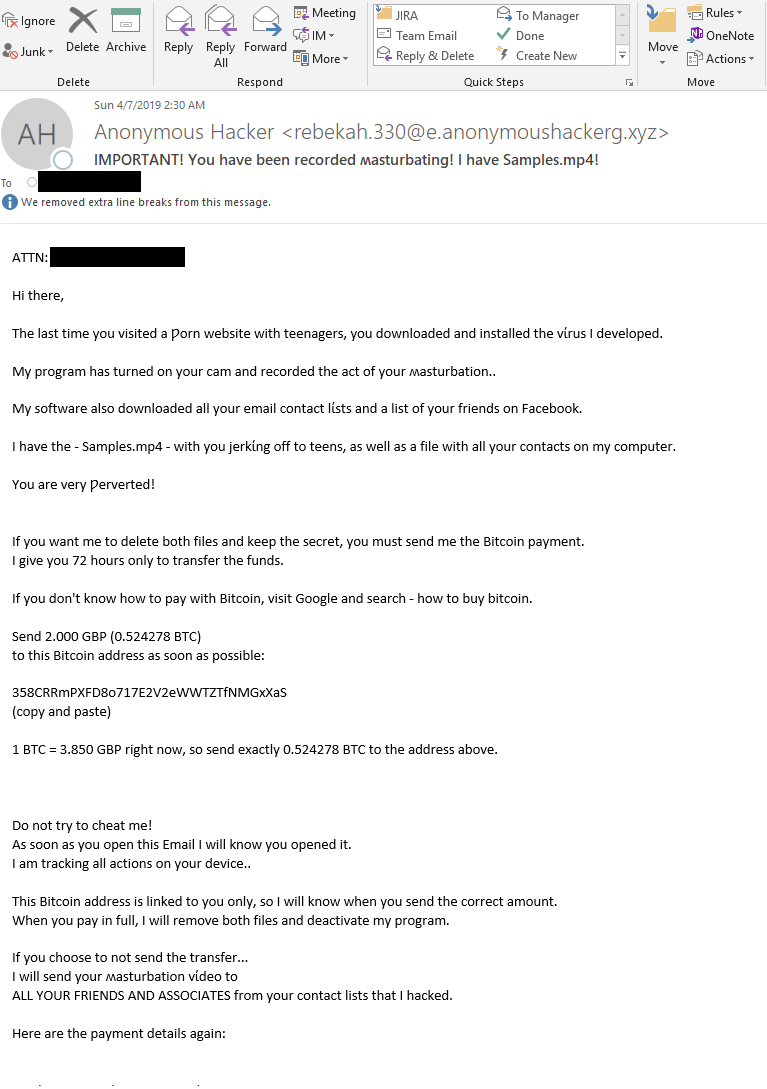
The scammer goes on to claim they have downloaded the victim’s contact list and Facebook friends and threatens to share footage of the victim “jerking off to teens” with those contacts – unless the scammer receives prompt payment in Bitcoin.
“In order to conceal the compromising materials, the attacker asks for a sum of around 0.43-0.45 Bitcoin – US $2000, however, we’ve already seen other messages asking for other amounts,” explains Ondrej Kubovic, ESET Security Awareness Specialist.
“The victim is directed to pay within 48 hours of opening the email or the cybercriminal threatens to send the incriminating video to all the contacts he/she has managed to steal from the infected device,” adds Kubovič.
Obsfucating words
Notably, the email obfuscates words that would normally be flagged by most anti-spam filters with non-Latin characters, all while keeping the meaning clear, such as “porn” and “masturbation”.
Jake Moore, cybersecurity specialist at ESET UK, said that sending the scam in multiple languages gives the sextortion emails a “false validity” that the scam is real and “targeted at the victim personally”.
“Before now, many have been in, albeit sometimes terrible, English,” he tells Verdict.
Moore says there is “little evidence” to suggest who is behind the sextortion emails, or their location.
“However, viewing the crypto wallets will show that many people have already deposited money into these digital accounts to silent such fake claims, although this is as far as such research will allow,” he says.
This latest scam follows a similar blueprint to countless other sextortion emails, although other techniques can vary, such as creating a fake social media profile and socially engineering a victim into sending compromising pictures before blackmailing them.
What to do if you receive a sextortion scam email?
If you find a sextortion email in your mailbox, Kubovič advises a calm response – the scammer is creating a sense of fear in order to make you act rashly.
“First of all, do not reply to the scam, do not download its attachments, do not click on embedded lines, and certainly do not send money to attackers.”
In previous sextortion campaigns, the scammer has claimed to know the victim’s password to convince the victim that their device has been hacked. However, it is likely that the attacker obtained the data from one of the many data leaks that included authentic passwords and logins.
“Indeed, in many cases, attackers actually test the login information and use the hacked account at least to spread their messages,” says Kubovič.
And because many people reuse the same password across multiple services, victims can be scared into paying the ransom.
“If an attacker lists your actual password, I recommend changing it and activating two-factor authentication on that service,” adds Kubovič.
The scammers can also spoof their email address, making it appear as though it has come from the victim’s own account, furthering the lie that they had been hacked.
“You should never pay accounts from a cold call email even if the content may drive you to fear the worst,” says Moore. “Hackers use such powers of influence to make victims act before they think but once the money has gone, it is usually untraceable and won’t be seen again.”
“Also, scan your device with reliable security software that can detect real infections and other issues, such as the misuse of the built-in webcam,” says Kubovič.
“This can be done, for example, by simply adding tape over its lens.”
Read more: London Blue scammers target Asia with BEC campaigns






