The technology industry continues to be a hotbed of patent innovation. Activity is driven by the need for stronger and more comprehensive cybersecurity measures to protect against cyber threats and attacks, and growing importance of technologies such as biometric recognition, machine learning, artificial intelligence, behavioral analytics, and multi-factor authentication. These technologies work in combination to establish a continuous and adaptive authentication process, ensuring that user identities are verified and protected throughout their interactions with digital systems. In the last three years alone, there have been over 4.1 million patents filed and granted in the technology industry, according to GlobalData’s report on Cybersecurity in technology: continuous authentication. Buy the report here.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
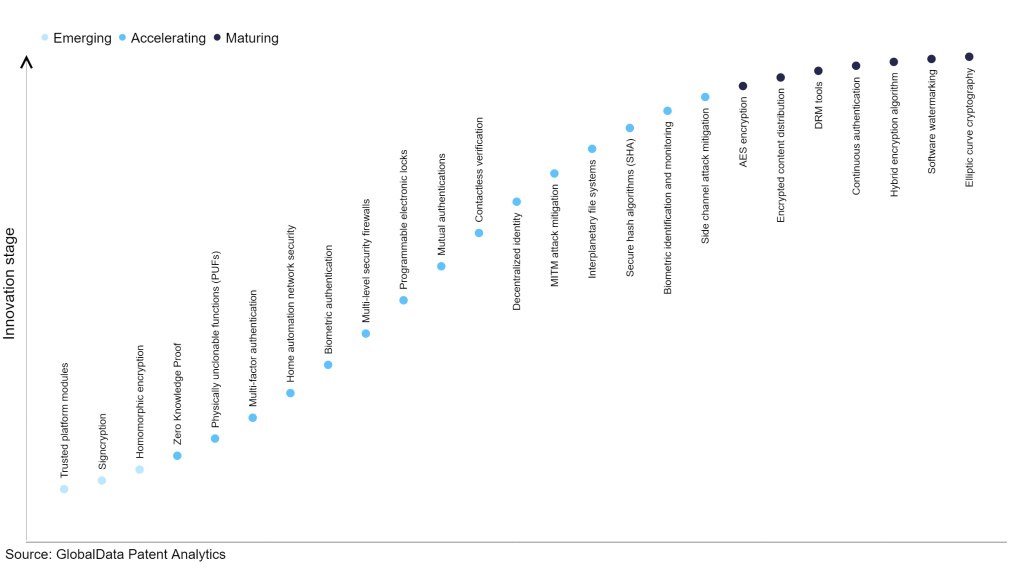
However, not all innovations are equal and nor do they follow a constant upward trend. Instead, their evolution takes the form of an S-shaped curve that reflects their typical lifecycle from early emergence to accelerating adoption, before finally stabilizing and reaching maturity.
Identifying where a particular innovation is on this journey, especially those that are in the emerging and accelerating stages, is essential for understanding their current level of adoption and the likely future trajectory and impact they will have.
190+ innovations will shape the technology industry
According to GlobalData’s Technology Foresights, which plots the S-curve for the technology industry using innovation intensity models built on over 1.5 million patents, there are 190+ innovation areas that will shape the future of the industry.
Within the emerging innovation stage, trusted platform modules, signcryption, and homomorphic encryption, are disruptive technologies that are in the early stages of application and should be tracked closely. Zero knowledge proof, physically unclonable functions (PUFs), and multi-factor authentication are some of the accelerating innovation areas, where adoption has been steadily increasing. Among maturing innovation areas are AES encryption and encrypted content distribution, which are now well established in the industry.
Innovation S-curve for cybersecurity in the technology industry
Continuous authentication is a key innovation area in cybersecurity
Continuous authentication is an ongoing verification process that employs various techniques to constantly confirm a user's identity. It is an automated procedure that validates a user's identity in real-time during their interactions with a system or network. By implementing continuous authentication, organizations can maintain strict control over access to sensitive systems and data, ensuring that only authorized individuals are granted entry. This approach incorporates methods such as biometric authentication, behavior analysis, location tracking, and other technologies that aid in verifying a user's identity.
GlobalData’s analysis also uncovers the companies at the forefront of each innovation area and assesses the potential reach and impact of their patenting activity across different applications and geographies. According to GlobalData, there are 440+ companies, spanning technology vendors, established technology companies, and up-and-coming start-ups engaged in the development and application of continuous authentication.
Key players in continuous authentication – a disruptive innovation in the technology industry
‘Application diversity’ measures the number of applications identified for each patent. It broadly splits companies into either ‘niche’ or ‘diversified’ innovators.
‘Geographic reach’ refers to the number of countries each patent is registered in. It reflects the breadth of geographic application intended, ranging from ‘global’ to ‘local’.
Sony Group is one of the leading patent filers in continuous authentication. The company’s patents are aimed at smart wearable devices and methods disclosed for providing feedback for optimal placement of the wearable device. This includes systems and methods to lock or unlock a wearable device and/or notify external wearable/non-wearable devices depending on the states of the wearer by sending notification or providing feedback if mispositioned or repositioned on the wearer.
It also includes systems and methods for providing a user indication of proper placement of a wearable device by providing feedback based on acquired bio-signal quality. In one embodiment, bio-signal quality is acquired by comparing a computed signal to noise ratio to that of an expected signal.
Other prominent patent filers in the continuous authentication space include Samsung, Microsoft, and Qualcomm.
By geographic reach, Autotrader leads the pack, followed by Avago Technologies International and Sony . In terms of application diversity, FaceTec holds the top position, followed by Autotrader, and Intertrust Technologies.
Continuous authentication offers a proactive and robust security approach, providing benefits such as enhanced security, user convenience, adaptive risk management, real-time threat detection, compliance support, fraud prevention, scalability, and user confidence.
To further understand how cybersecurity is disrupting the technology industry, access GlobalData’s latest thematic research report on Cybersecurity.
Data Insights
From

The gold standard of business intelligence.
Blending expert knowledge with cutting-edge technology, GlobalData’s unrivalled proprietary data will enable you to decode what’s happening in your market. You can make better informed decisions and gain a future-proof advantage over your competitors.






