The technology industry continues to be a hotbed of patent innovation. Activity is driven by the surge in digital content consumption, the need for content creators to monetize their work, and the increasing threat of online piracy, and growing importance of technologies such as blockchain and watermarking techniques. In the last three years alone, there have been over 1.5 million patents filed and granted in the technology industry, according to GlobalData’s report on Cybersecurity in technology: DRM tools. Buy the report here.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
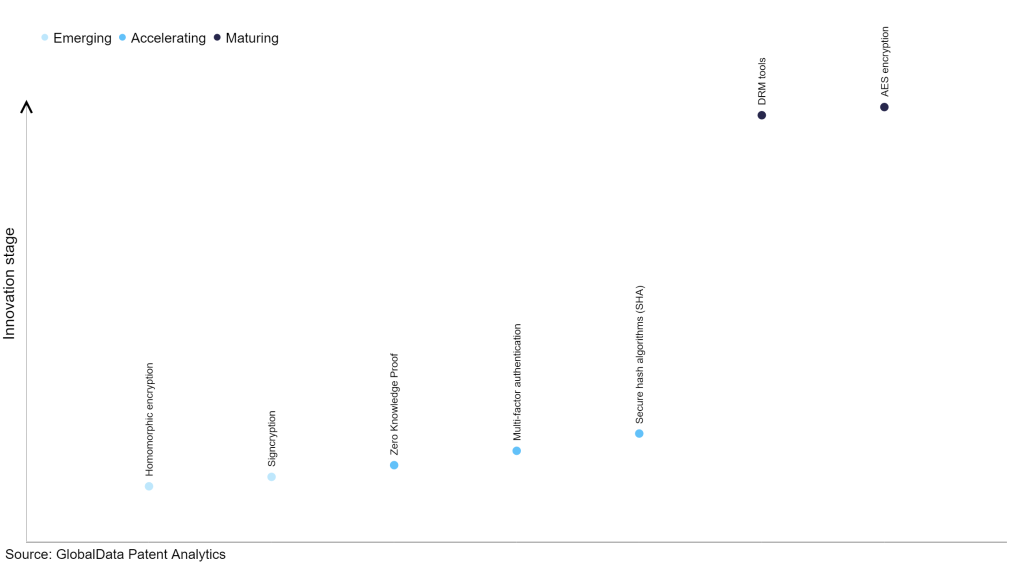
However, not all innovations are equal and nor do they follow a constant upward trend. Instead, their evolution takes the form of an S-shaped curve that reflects their typical lifecycle from early emergence to accelerating adoption, before finally stabilizing and reaching maturity.
Identifying where a particular innovation is on this journey, especially those that are in the emerging and accelerating stages, is essential for understanding their current level of adoption and the likely future trajectory and impact they will have.
185+ innovations will shape the technology industry
According to GlobalData’s Technology Foresights, which plots the S-curve for the technology industry using innovation intensity models built on over 1.6 million patents, there are 185+ innovation areas that will shape the future of the industry.
Within the emerging innovation stage, homomorphic encryption and signcryption are disruptive technologies that are in the early stages of application and should be tracked closely. Zero knowledge proof, multi-factor authentication and secure hash algorithms (SHA) are some of the accelerating innovation areas, where adoption has been steadily increasing. Among maturing innovation areas are DRM tools and AES encryption, which are now well established in the industry.
Innovation S-curve for cybersecurity in the technology industry
DRM tools is a key innovation area in cybersecurity
Digital rights management tools are software or systems engineered to safeguard and oversee digital content and intellectual property rights. They guarantee that copyrighted materials are distributed and accessed securely, shielding them from unauthorized use. DRM tools rely on encryption, licensing, and access control mechanisms to protect digital assets, thwart piracy, and regulate the usage rights of content.
GlobalData’s analysis also uncovers the companies at the forefront of each innovation area and assesses the potential reach and impact of their patenting activity across different applications and geographies. According to GlobalData, there are 275+ companies, spanning technology vendors, established technology companies, and up-and-coming start-ups engaged in the development and application of DRM tools.
Key players in DRM tools – a disruptive innovation in the technology industry
‘Application diversity’ measures the number of applications identified for each patent. It broadly splits companies into either ‘niche’ or ‘diversified’ innovators.
‘Geographic reach’ refers to the number of countries each patent is registered in. It reflects the breadth of geographic application intended, ranging from ‘global’ to ‘local’.
Among the companies innovating in cybersecurity-enabled DRM tools, Sony Group is one of the leading patents filers. The company’s patents are aimed at describing an information processing device comprising a data processing unit that plays back content stored in a medium. The medium contains a general-purpose area holding encrypted content and utilization control data linked to the content, as well as a protected area with restricted access blocks. These blocks encompass a title key storage section holding an encryption key for deciphering the content and time validity details pertaining to the application of the encryption key to the content.
Additionally, it includes a status storage segment recording the date of initial content playback. The data processing unit retrieves the validity period data indicating the duration for which content usage is permitted, determined by the date of the first content playback from the title key storage block. It then assesses whether content playback is permissible based on a comparison between the obtained validity period data and the current date information. Other prominent patent filers in the space include Microsoft and Samsung Group.
In terms of application diversity, Sony Group leads the pack, while Microsoft and Samsung Group are in second and third positions, respectively. By means of geographic reach, Videri held the top position, followed by EcoStar and Virtru.
Cybersecurity is crucial in DRM tools as it forms the bedrock of content protection. These tools are designed to safeguard digital assets and intellectual property, ensuring they are accessed and distributed securely. Effective cybersecurity measures, such as encryption protocols and secure authentication methods, are vital in preventing unauthorized access, piracy, and illegal distribution of copyrighted materials.
To further understand the key themes and technologies disrupting the technology industry, access GlobalData’s latest thematic research report on Cybersecurity.
Data Insights
From

The gold standard of business intelligence.
Blending expert knowledge with cutting-edge technology, GlobalData’s unrivalled proprietary data will enable you to decode what’s happening in your market. You can make better informed decisions and gain a future-proof advantage over your competitors.