The technology industry continues to be a hotbed of patent innovation. Activity is driven by the escalating need for robust security measures in areas such as IoT, hardware authentication, and secure key storage, as well as the increasing awareness of PUFs’ resistance to attacks, and growing importance of technologies such as semiconductor manufacturing processes, PUF circuit designs, and cryptographic algorithms, collectively driving advancements in PUF-based cybersecurity solutions. In the last three years alone, there have been over 4.1 million patents filed and granted in the technology industry, according to GlobalData’s report on Cybersecurity in technology: physically unclonable functions (PUFs). Buy the report here.
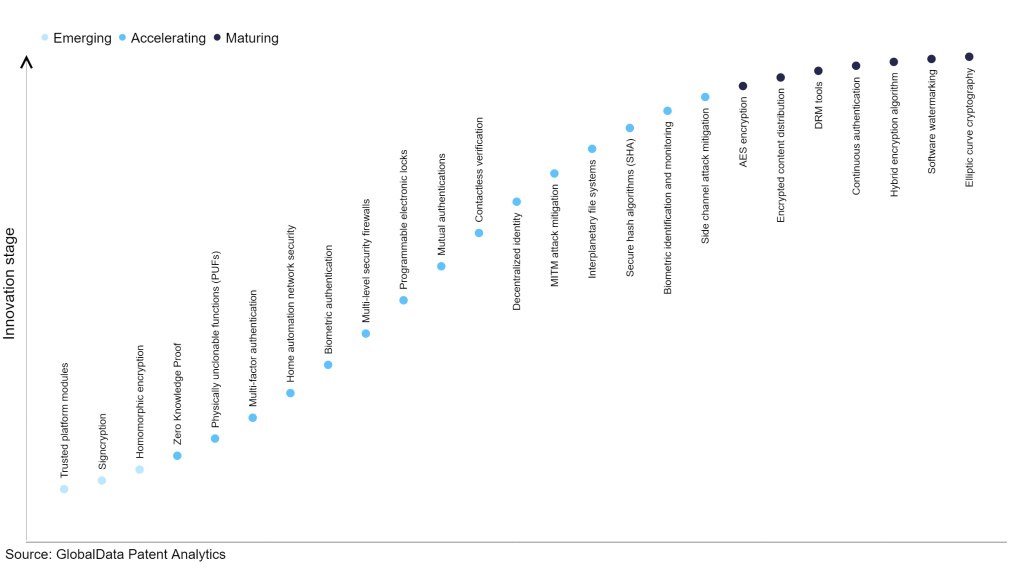
However, not all innovations are equal and nor do they follow a constant upward trend. Instead, their evolution takes the form of an S-shaped curve that reflects their typical lifecycle from early emergence to accelerating adoption, before finally stabilizing and reaching maturity.
Identifying where a particular innovation is on this journey, especially those that are in the emerging and accelerating stages, is essential for understanding their current level of adoption and the likely future trajectory and impact they will have.
190+ innovations will shape the technology industry
According to GlobalData’s Technology Foresights, which plots the S-curve for the technology industry using innovation intensity models built on over 1.5 million patents, there are 190+ innovation areas that will shape the future of the industry.
Within the emerging innovation stage, trusted platform modules, signcryption, and homomorphic encryption are disruptive technologies that are in the early stages of application and should be tracked closely. Side channel attack mitigation, biometric identification and monitoring, and secure hash algorithm (SHA) are some of the accelerating innovation areas, where adoption has been steadily increasing. Among maturing innovation areas are elliptic curve cryptography, software watermarking, and hybrid encryption algorithm, which are now well established in the industry.
Innovation S-curve for cybersecurity in the technology industry
Physically unclonable functions (PUFs) is a key innovation area in cybersecurity
Physically uncloneable functions (PUFs) represent a security technology employing distinctive physical attributes of devices to establish authentication. By generating a response to a challenge rooted in the device's singular physical traits influenced by manufacturing differences, PUFs ensure the device cannot be replicated, thus enabling secure authentication.
GlobalData’s analysis also uncovers the companies at the forefront of each innovation area and assesses the potential reach and impact of their patenting activity across different applications and geographies. According to GlobalData, there are 80+ companies, spanning technology vendors, established technology companies, and up-and-coming start-ups engaged in the development and application of physically unclonable functions (PUFs).
Key players in physically unclonable functions (PUFs) – a disruptive innovation in the technology industry
‘Application diversity’ measures the number of applications identified for each patent. It broadly splits companies into either ‘niche’ or ‘diversified’ innovators.
‘Geographic reach’ refers to the number of countries each patent is registered in. It reflects the breadth of geographic application intended, ranging from ‘global’ to ‘local’.
Patent volumes related to physically unclonable functions (PUFs)
| Company | Total patents (2010 - 2022) | Premium intelligence on the world's largest companies |
| eMemory Technology | 48 | Unlock Company Profile |
| Qualcomm | 61 | Unlock Company Profile |
| Thales | 15 | Unlock Company Profile |
| Lexmark International | 42 | Unlock Company Profile |
| Siemens | 71 | Unlock Company Profile |
| Rambus | 18 | Unlock Company Profile |
| Synopsys | 12 | Unlock Company Profile |
| NXP Semiconductors | 30 | Unlock Company Profile |
| Taiwan Semiconductor Manufacturing | 36 | Unlock Company Profile |
| Fraunhofer-Gesellschaft zur Forderung der Angewandten Forschung | 17 | Unlock Company Profile |
| Alibaba Group | 50 | Unlock Company Profile |
| SRI International | 16 | Unlock Company Profile |
| Semiconductor Manufacturing International | 11 | Unlock Company Profile |
| Emsycon | 17 | Unlock Company Profile |
| Renesas Electronics | 37 | Unlock Company Profile |
| Mitsubishi Electric | 76 | Unlock Company Profile |
| Winbond Electronics | 23 | Unlock Company Profile |
| Everspin Technologies | 15 | Unlock Company Profile |
| Sony Group | 18 | Unlock Company Profile |
| Advanced New Technologies | 14 | Unlock Company Profile |
| Nippon Telegraph and Telephone | 16 | Unlock Company Profile |
| IBM | 86 | Unlock Company Profile |
| STMicroelectronics | 16 | Unlock Company Profile |
| TTP | 15 | Unlock Company Profile |
| Macronix International | 36 | Unlock Company Profile |
| KDDI | 11 | Unlock Company Profile |
| Toshiba | 18 | Unlock Company Profile |
| Intel | 123 | Unlock Company Profile |
| Spectra Systems | 16 | Unlock Company Profile |
| Micron Technology | 18 | Unlock Company Profile |
| Zwipe | 12 | Unlock Company Profile |
| Arizona Board of Regents | 22 | Unlock Company Profile |
| Intrinsic-ID | 40 | Unlock Company Profile |
| European Union | 11 | Unlock Company Profile |
| Quantum Base | 39 | Unlock Company Profile |
| Crypto Quantique | 18 | Unlock Company Profile |
| Secure-IC | 18 | Unlock Company Profile |
Source: GlobalData Patent Analytics
Among the companies innovating in physically unclonable functions, Intel is one of the leading patents filers. The company’s patents are aimed at a method for securely providing secret keys in the manufacturing of integrated circuits through fuse attestation. An apparatus is outlined, comprising elements such as a storage location, a physically unclonable function (PUF) circuit, a PUF key generator, an encryption unit, and multiple fuses. These components work in tandem. The PUF circuit generates a unique value, the PUF key generator processes it into a PUF key, and the encryption unit encrypts a configuration fuse value. Both the PUF key and the configuration fuse value are sent to a key server. Upon confirming that the configuration fuse value designates the apparatus as a production component, the key server furnishes a fuse key to be stored in the array of fuses.
Other prominent patent filers in the space include IBM and Mitsubishi Electric.
In terms of application diversity, Everspin Technologies held the top position, while eMemory Technology and Macronix International stood in second and third positions, respectively. By means of geographical reach, eMemory Technology leads the pack, followed by Emsycon and Alibaba Group.
PUFs play a critical role in cybersecurity by leveraging the unique physical properties of hardware components to generate cryptographic keys or identifiers. These keys are virtually impossible to duplicate, providing an exceptionally robust defence against unauthorized access, counterfeiting, and attacks on sensitive information, thereby fortifying the security of various systems and applications.
To further understand the key themes and technologies disrupting the technology industry, access GlobalData’s latest thematic research report on Cybersecurity.
Premium Insights
From

The gold standard of business intelligence.
Blending expert knowledge with cutting-edge technology, GlobalData’s unrivalled proprietary data will enable you to decode what’s happening in your market. You can make better informed decisions and gain a future-proof advantage over your competitors.