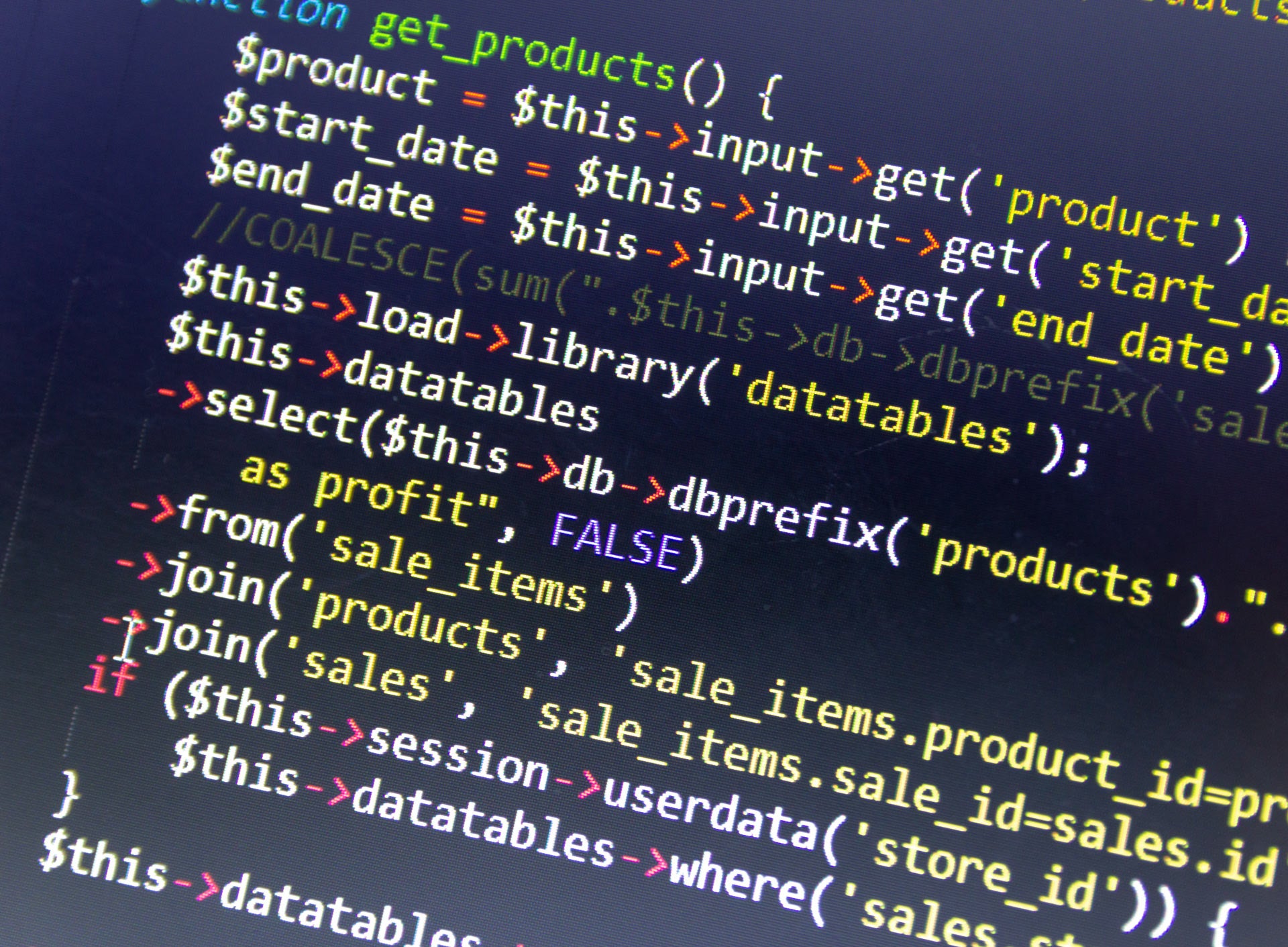
PHP, the programming language used by 80% of the world’s websites, is becoming increasingly vulnerable to cyberattacks, security researchers have warned, with PHP attacks on the rise.
In research published today by F5 Labs, PHP was identified as the target of 81% of the web’s malicious traffic in 2018, representing a 23% rise on 2017.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
The report, entitled Application Protection Report 2019, also found that PHP accounts for 68% of the exploits published in 2018 on the Exploit Database – a repository of the known software weakpoints that can be used by cyberattackers.
“The volume and relentless nature of PHP exploits are alarming but unsurprising,” said Sander Vinberg, Threat Research Evangelist, F5 Labs.
“Based on our research, we predict that it will remain one of the internet’s weakest links and broadest attack surfaces for the foreseeable future.”
Admin rights at the core of PHP attacks
Perhaps the biggest reason for PHP attacks seeing such growth is the programming language’s role in the administrative access of the majority of the world’s websites.
One of the most common ways to manage and maintain user access to website’s content management systems, for example, is through MySQL databases, which are typically managed through a PHP web application known as phpMyAdmin (PMA).
Successful access to this can give hackers the keys to an entire online system, making it a hugely popular target.
Data provided to F5 Labs by its partner Loryka found that 42% of 1.5 million events targeting 100,000 different URLs were aimed at those concerning PMA access.
On closer inspection, 87% of this traffic was found to stem from just two IPs, which together represent an incredible 37% of all monitored traffic in 2018. It appears to indicate a campaign to gain access to the admin rights of a host of websites, and while the perpetrators have not been identified, F5 has determined that both IPs come from systems on a single university campus in North America.
“Basically, unknown actors used a small number of compromised systems on university networks to look for specific targets: old and probably neglected MySQL databases with weak authentication,” explained Vinberg.
“These actors have defined a narrow set of target parameters but are scanning the entire web from a small number of addresses – and are not trying too hard to cover their tracks. Given that SQL injection was the most common PHP attack, it seems that the threat landscape is going to look similar this year.”
Read more: 4 in 5 IT chiefs are delaying security patches to avoid business disruption







