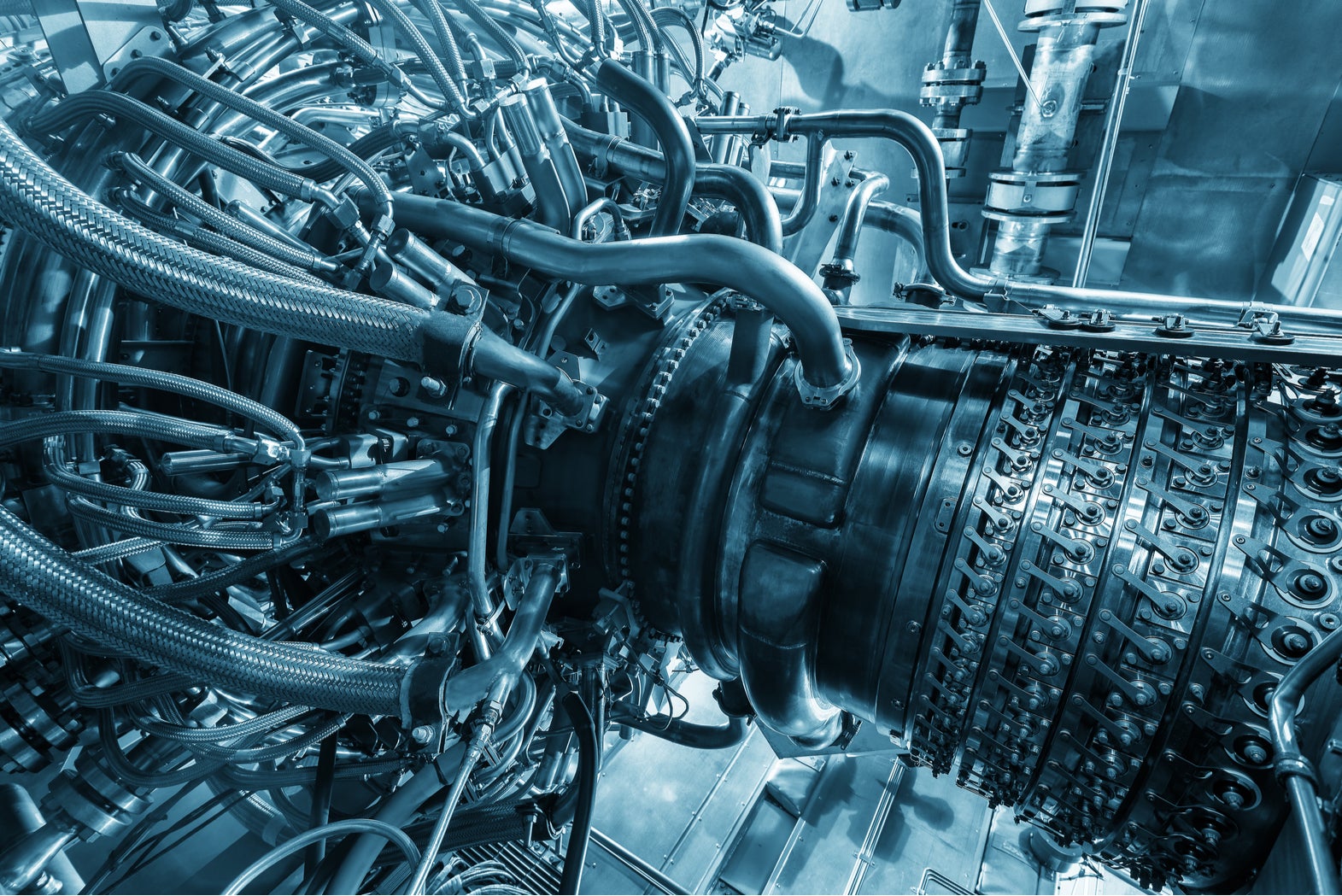
ASCO is the latest manufacturing giant to be targeted with ransomware by cybercriminals, which has forced the world’s largest airplane parts manufacturer to halt production.
According to reports, ASCO has been struggling to deal with the infection since Friday, 7 June, and has been forced to send home 1,000 of its 1,400 employees due to the spread of the ransomware. It was hoped that employees would be able to return to work today, but the company has since reportedly extended the downtime until next Monday.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
The ransomware attack is believed to have spread around the company’s Zaventem plant in Belgium. However, production has also ceased in other offices in France and Brazil. It is unclear whether the virus has spread to other offices or ASCO has made the decision in order to stop this from occurring while it investigates.
It is unconfirmed which malware strain has infected the company’s systems. However, a string of industrial and manufacturing giants have been targeted by the LockerGoga ransomware of late. This ransomware strain is thought to be delivered through targeted phishing campaigns which trick employees into installing the malicious files on their system, allowing it to spread throughout the company network.
ASCO provides parts for many of the leading companies in the aviation industry, including Boeing, Airbus, Bombardier and Lockheed Martin.
ASCO ransomware attack doesn’t have to cause long-term damage
Norsk Hydro, a leading aluminium producer, was recently hit by a similar attack that forced it to shut down production, costing the company $40m in losses. Despite that, the company saw its share price grow in the month following the attack.
According to Shlomie Liberow, technical program manager at HackerOne, this was a result of Norsk Hydro’s swift reaction to and reporting of the incident.
“Norsk showed the world that while ransomware is costly and devastating in the moment, it doesn’t have to have a lasting effect on reputation as the open and transparent way Norsk dealt with the attack resulted in a rise in share price,” Liberow said.
The company was quick to admit that its IT systems were under attack, and immediately began working with Norway’s National Security Authority (NSM) to determine the extent of the attack and whether there was any further risk. With a similar response, Liberow believes that ASCO could also overcome the attack without suffering substantial long-term damage:
“Public understanding of ransomware is on the rise so if ASCO reacts quickly and in a way that keeps relevant stakeholders informed, hopefully it will see no lasting damage to reputation.”
Andrea Carcano, CPO of Nozomi Networks, agrees. According to Carcano, organisations should know what to do and be ready to spring into action should they come under attack, not only to limit disruption to production, but also to protect against reputational damage:
“Organisations should prepare for these types of events and have an incident response plan in place to help limit the damage caused, not only to production but also to customer trust and brand reputation.”
“Prevention is always better than cure”
However, both Carcano and Liberow agree that businesses should aim to prevent against these attacks, rather than waiting for an attack to occur.
Businesses can protect themselves from ransomware attacks by simply ensuring that all systems are up to date with the latest security patches installed and there are no security vulnerabilities that “could leave an organisation exposed to attackers,” Liberow explained.
However, given that many of these attacks appear to be targeted, more advanced cybersecurity solutions, such as those that make use of artificial intelligence technologies, may be needed to keep an organisation protected.
According to Carcano, organisations need tools that will detect ambiguous activity within the company infrastructure, allowing a response before attackers are successfully able to breach their systems:
“Applying artificial intelligence and machine learning for real-time detection and response, organisations can monitor for malware to rapidly discover and act to remove malicious code and the risks posed before harm is done.”
Read more: Insider threat: 25% of us would sell out our employers for just £1,000







