Services from wearable device maker Garmin are still down following a ransomware attack on Thursday.
The company was forced to shut down its services on 23 July after it was hit by a ransomware attack that encrypted its internal network.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
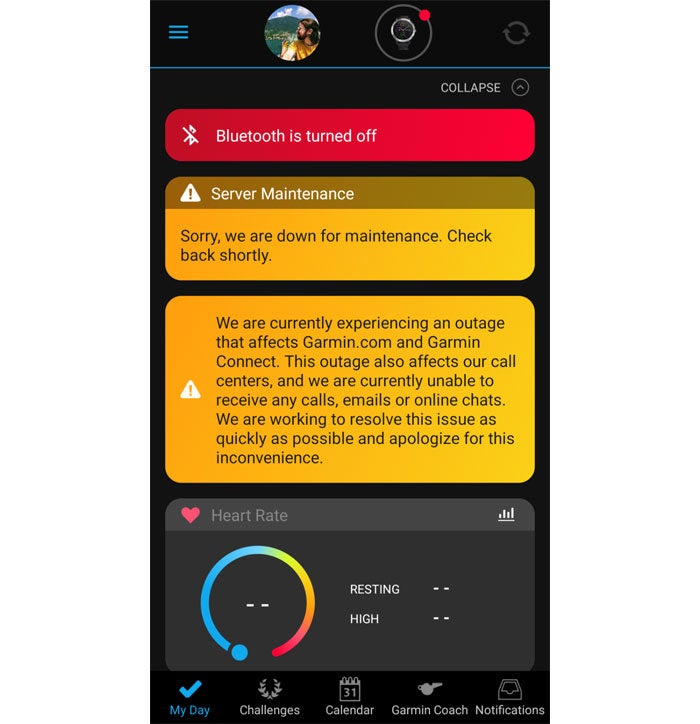
Garmin Connect, the service that enables users to sync their data, is among the services that are down. Also affected is the Garmin store, the company’s email servers, call centres and online chat tool and its production line in Taiwan. Its flyGarmin brand, which supplies navigation equipment to the aviation equipment has also been impacted.
It has been suggested that the strain of ransomware causing the incident is WastedLocker, although this has not been confirmed and it is currently not known who is responsible.
Users with Garmin devices are currently being served with the message:
“We are currently experiencing an outage that affects Garmin.com and Garmin Connect. This outage also affects our call centres, and we are currently unable to receive any calls, emails or online chats. We are working to resolve this issue as quickly as possible and apologise for this inconvenience.”
Garmin is the latest in a long line of companies to be severely impacted by ransomware, which according to SonicWall’s 2020 Mid-Year Threat Report, has seen a 20% increase globally in the first half of 2020.
 Garmin down following ransomware attack: Potentially severe implications
Garmin down following ransomware attack: Potentially severe implications
Garmin has not provided any timeframe for when the ransomware attack, and the service outages, will be resolved. It is likely that it has been asked to pay a ransom, although paying is generally not advisable as it can mark the payee as an easy target for repeat attacks.
It is also unclear if any personal data has been stolen as part of the attack, although it is possible. And if this is the case, there are potentially severe implications due to the collective value of such rich location data for so many users, particularly for bad actors.
“If the attackers made a copy of all user’s location data history, they would have no problems finding buyers from various intelligence agencies,” tweeted F-Secure CRO Mikko Hypponen, commenting on the Garmin ransomware attack.
Fitness trackers have previously proved to be an embarrassing source of insight into top-secret operations.
For example, in 2018 fitness tracking app Strava became an unintentional leak vector for sensitive information about the location and staffing of secret US military bases when soldiers uploaded their run data, which was shared as data visualisations with other users.
The attack also highlights the dangers of ransomware attacks to companies, which are particularly exposed with so many employees working from home.
“Remote and mobile workforces are at a turning point on the subject of security,” said Chad Sweet, founder and CEO The Chertoff Group.
“It has never been more prevalent for enterprises and organisations to prioritise online security and make what used to be a luxury, a secured and protected necessity.”
Read more: Number of UK organistions paying ransomware has doubled: CrowdStrike