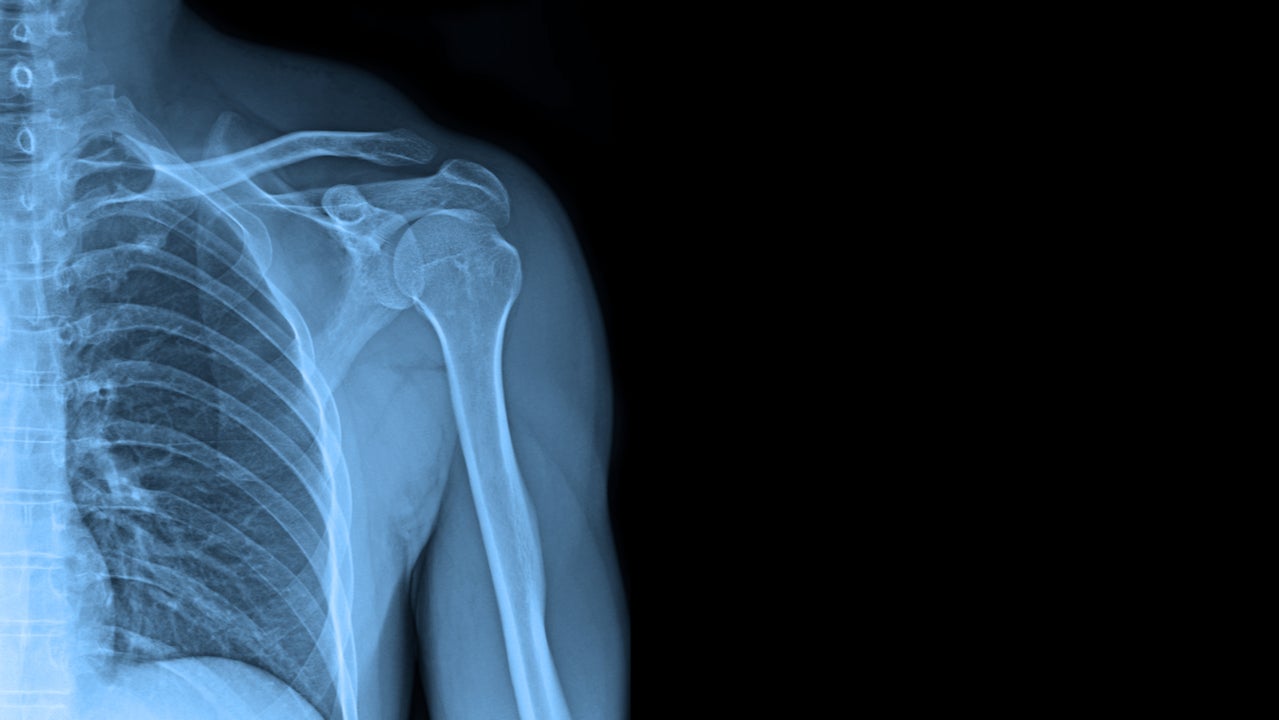
Cybersecurity researchers have discovered more than 45 million medical images, including X-rays and CT scans, exposed online without encryption or password protection.
Each freely accessible medical image file is linked to up to 200 lines of metadata, which include personally identifiable information such as name, address and birth date.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
Images were also tied to sensitive personal healthcare information including diagnosis, height and weight. The researchers warn that this “highly personal” data could end up in the hands of cybercriminals via the dark web, possibly leading to fraud, extortion or ransomware.
During a six-month investigation into the data storage systems used by healthcare organisations, digital risk firm CybelAngel scanned approximately 4.3 billion IP addresses for insecure servers.
The company discovered more than 2,140 unprotected healthcare servers spread across 67 countries, including the US, UK and Germany.
In some cases, healthcare portals could be accessed without entering a username or password.
“The fact that we did not use any hacking tools throughout our research, highlights the ease with which we were able to discover and access these files,” said David Sygula, senior cybersecurity analyst at CybelAngel and one of the researchers who discovered the medical images.
Medical images exposed: A long-running problem
CybelAngel focused their investigation on network-attached storage servers and Digital Imaging and Communications in Medicine, the standard used by healthcare professionals for managing medical imaging data.
The medical images exposure was not caused by a singular organisation or IT system, but rather by widespread security “gaps” and poor data practices. As such, it was not possible for CybelAngel to contact every organisation that was leaking medical images.
Todd Carroll, CybelAngel CISO, said: “Medical centres work with a vast, interconnected web of third-party providers and the cloud is an essential platform for sharing and storing data. However, gaps in security, such as this, present a huge risk, both for the individuals whose data is compromised and the healthcare institutions that are governed by regulations to protect patients’ data.
“The health sector has faced unprecedented challenges this year, however the security and privacy of their patients’ most personal records must be protected, to prevent highly confidential data falling into the wrong hands.”
It is not the first time researchers have uncovered hordes of unprotected medical images. In January this year, Germany-based security firm Greenbone Networks discovered more than a billion medical images available on an insecure storage system for anyone to access.
Healthcare organisations exposing medical images are liable for sanctions under data protection laws. Under GDPR, health data is deemed a ‘special category’, which means organisations storing it must carry out a data protection impact assessment.
“This is a concerning discovery and proves that more stringent security processes must be put in place to protect how sensitive medical data is shared and stored by healthcare professionals,” added Sygula.
“A balance between security and accessibility is imperative to prevent leaks from becoming a major data breach.”
Read more: Vaccine documents hacked in European Medicines Agency cyberattack







