
According to data breach tracker Have I Been Pwned, more than five billion account credentials have been accessed and stolen in large-scale attacks. More than 70,000 data sets have been posted online containing the emails, passwords, names and web activity of more than 75 million people. There is a high chance that your details are out there somewhere too.
With popular websites like LinkedIn, Yahoo and MySpace having suffered attacks in the past, in which hundreds of millions of email addresses and passwords are believed to have been stolen, people continue to be careless when it comes to internet security.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
According to a study conducted by password manager app Dashlane, we continue to make it easy for hackers to access our accounts by using the same guessable passwords over and over again.
The researchers looked at 61.5 million passwords previously gathered by the Department of Computer Science at Virginia Tech to study the trends in password creation.
The most common passwords
Dashlane’s research showed that many of us are still using our pop culture interests, such as sports, brands, movies and music, to create our passwords.
Myspace, Mustang, Superman and Slipknot were among the most commonly used passwords.
Car brands, such as Ferrari, Mercedes and Corvette all feature, as do food-related passwords such as cocacola, snickers and skittles.
Likewise, sport also proves popular, with Liverpool, Chelsea, Arsenal, Barcelona and Manchester among the most frequently used passwords.
If we’re not using sports team, bands, movies and brands as password inspiration, we’re using commonly used phrases like iloveyou and fu**you. As you may have noticed, these phrases tend to be either love or hate, with little in between. A**hole, fu**off, iloveme, trustno1, beautiful, ihateyou, bullsh** and lovelove make up the top ten.
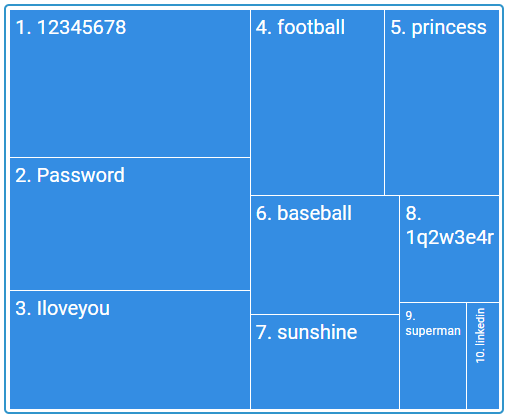
People were also found to be “password walking”, or using a combination of letters, numbers and symbols that appear next to each other on a keyboard. A particularly bad example would be 12345678 (found to be the most commonly used password), or a good example would be 1q2w3e4r5t6y.
According to Dashlane, the most common eight character password bases are as follows:
Reusing passwords
Simple, common passwords that are easy for hackers to guess are a huge security risk. One type of attack, a brute-force, sees a computer programme try an endless combination of letters, numbers and symbols until it finds the correct combination. These programmes can also be set to run through a list of commonly used passwords.
However, perhaps the most worrying trend is that people are still reusing the same password for multiple services.
Ryan Merchant, senior manager at Dashlane, told Verdict:
“The main security culprit that people can eliminate to keep their accounts more secure is password reuse. If you reuse a password for multiple accounts then all it takes is for one account to be breached in order for all of your accounts to be in grave danger.”
Dashlane research shows that the average internet user has more than 150 accounts, so it comes as little surprise that people are using the same password or creating slight variants for all of their accounts. However, they run the risk of having a hacker gain access to all of their online accounts.
Troy Hunt, the web security expert behind Have I Been Pwned, told Verdict:
“Reuse is the biggest problem. I say that because of the rapid emergence of credential stuffing attacks, which is when an attacker takes usernames and passwords from a data breach and tests them against other services.”
Essentially, after gaining access to one of your accounts, the hacker will then try to use your details to log in to other sites that may be more valuable to them. If you tend to reuse your password on multiple sites, a hacker gaining access to your Facebook account might give them what they need to access your PayPal account, which would undoubtedly be a far more significant threat.
How can you protect yourself?
Of course, it isn’t always a matter of users failing to create an adequate password. Many data breaches are a result of companies failing to protect their users’ data.
“Each breach is inherently different, but overall companies are doing a terrible job at both securing user data, as well as enforcing strong password policies,” Merchant told Verdict.
However, it is on the user to ensure that their accounts are secure. A strong password is the first line of defence.
Merchant said:
“We need to think of passwords as the seatbelts of the digital age. They are your first-line of defence to keep your accounts and personal information safe. A weak password leaves your identity, finances, and other personal information at risk to a host of terrible scenarios.
“It [a password] should be eight-plus characters and contain a random combination of letters, numbers and symbols.”
Password managers
Hunt also recommends creating randomly generated strings of letters, numbers and symbols that are almost impossible for hackers to crack. A unique string should be created for each new account that you create.
Using the name of your favourite celebrity may be memorable, but it’s also a very brittle line of defence.
“A password manager is the first step to keeping your online accounts safe. I’ve been using 1Password for many years now and all the passwords I have are randomly generated strings I then store in there,” Hunt told Verdict.
Password management software can be used to generate complex passwords which are then stored in an encrypted database. The only way to access these credentials is with your master password. While there is still an element of risk there, as gaining access to your password manager account would provide access to all of your other accounts, it generally means that your passwords are more complex and therefore more difficult to crack.
Likewise, most password managers come with two-factor authentication. This means that even if somebody does get into your account, they would require a second access code which is sent to a secondary device such as a smartphone.
Hunt told Verdict:
“I also use two factor authentication on everything possible so that even if someone else gets a password, they can’t access the account it belongs to.”







