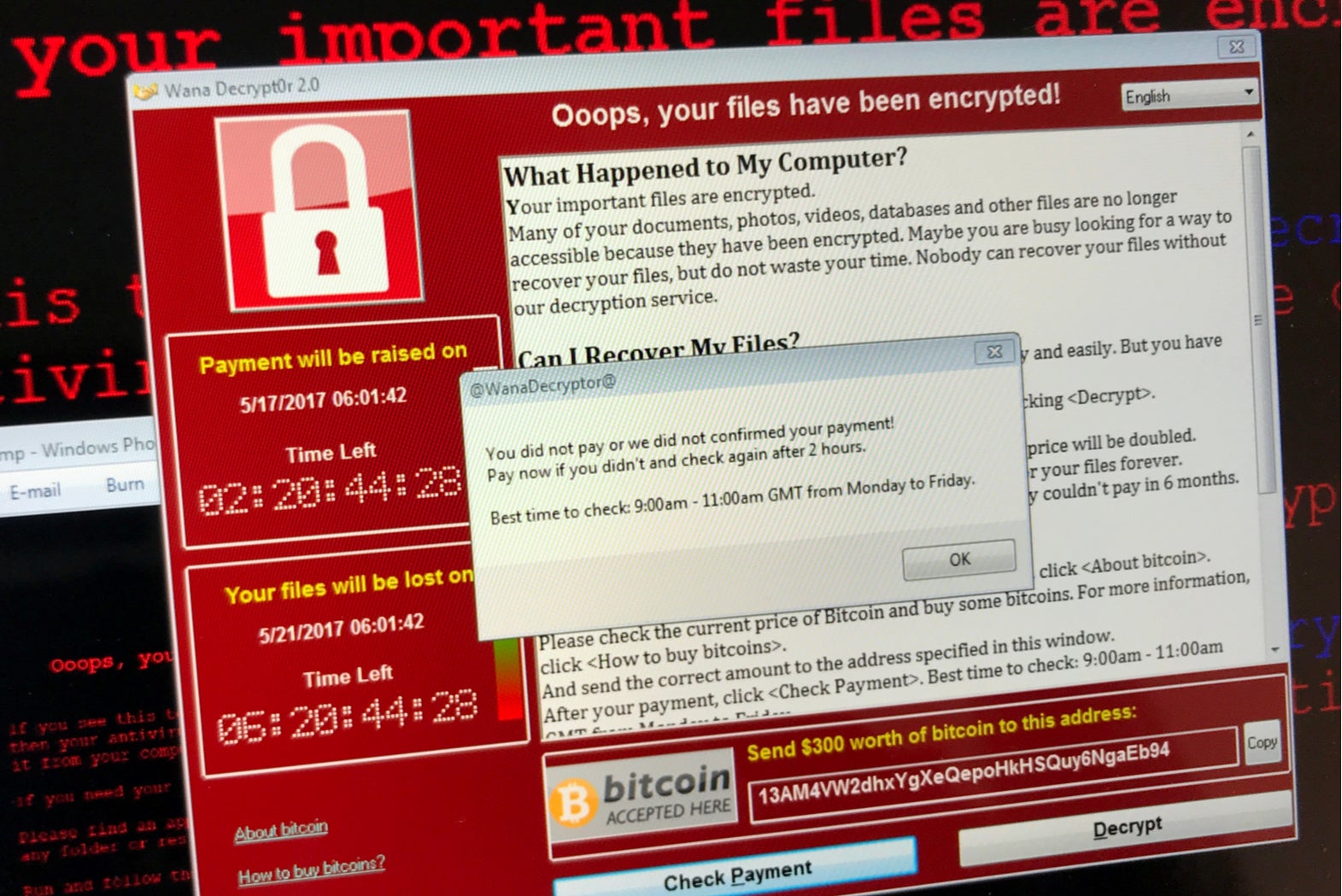
A new report has concluded that the United Kingdom’s NHS remains vulnerable to cyberattacks two years on the from WannaCry ransomware attack that cost the healthcare provider £92m in damages and lost productivity.
According to a new report on NHS Cyber Security by Imperial College London’s Institute of Global Health Innovation, outdated computer systems, lack of investment and the technology skills deficit has left the NHS open to further attacks.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
Likewise, the use of private technologies companies, who provide the NHS with IT services, is also leaving patient data vulnerable to breach or exploit.
The researchers point to breaches involving third party providers in the US such as Quest Diagonstics, which saw 12 million patient records exposed, as evidence of this. A similar breach involving healthcare diagnostics company LabCorp saw data belonging to 7.7 million patients exposed.
Likewise, Swedish healthcare information provider Swedish Healthcare Guide recently left 2.7 million patient telephone calls exposed on an unencrypted, publicly accessible server.
The high value of this data makes such providers potentially lucrative targets for cybercriminals or malicious insiders. However, the report concluded that there were “warning signs” to suggest that healthcare cloud providers are offering inadequate protection of patient data.
The report states that, similar to US providers, the NHS is also “completely reliant on third parties to store and protect their data”.
Protecting patients must come above cutting costs
Recent research by software company Veracode found that healthcare organisations are quicker to fix security flaws than any other industry. The healthcare industry took seven months to address the majority of vulnerabilities found in its software, compared to 15 months on average in other industries.
“In the wake of WannaCry, which attacked many organisations including the NHS, you’d think the security in place would have been stepped up to maximum strength,” Jake Moore, cybersecurity specialist at ESET, told Verdict.
Yet, while code quality is seemingly being addressed, cybersecurity still appears to be lacking – particularly due to the reliance on third party providers. And according to Moore, this could suggest that cost is being put ahead of protecting patients’ data from cybercriminals.
“More and more third party technology firms are brought into helping government organisations with their day to day work as outsourcing is seen as a cheaper option,” Moore said. “The main reason can sometimes be on cost alone which can inevitably put security and protection of the systems lower down the priority list.”
However, while the NHS may be making savings now, another attack “would be a disaster”, according to Moore, potentially costing more in damages than the savings currently being made. Therefore protecting patient data should be its number one priority “whatever the cost”.
The report has called for increased scrutiny of the cybersecurity practices of third party companies that hold confidential patient data.
Likewise, it has also suggested putting rules in place to ensure the development and use of emerging technologies such as artificial intelligence and robotics does not compromise security.
Read more: PCM data breach highlights risks of third-party cloud providers







