
When one thinks of comics they think of superheroes. Captain America, Batman, Spiderman, The Flash… those are the names we associate with comic books.
However, Syracuse University in New York, are telling a much more human story using the medium of comics.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
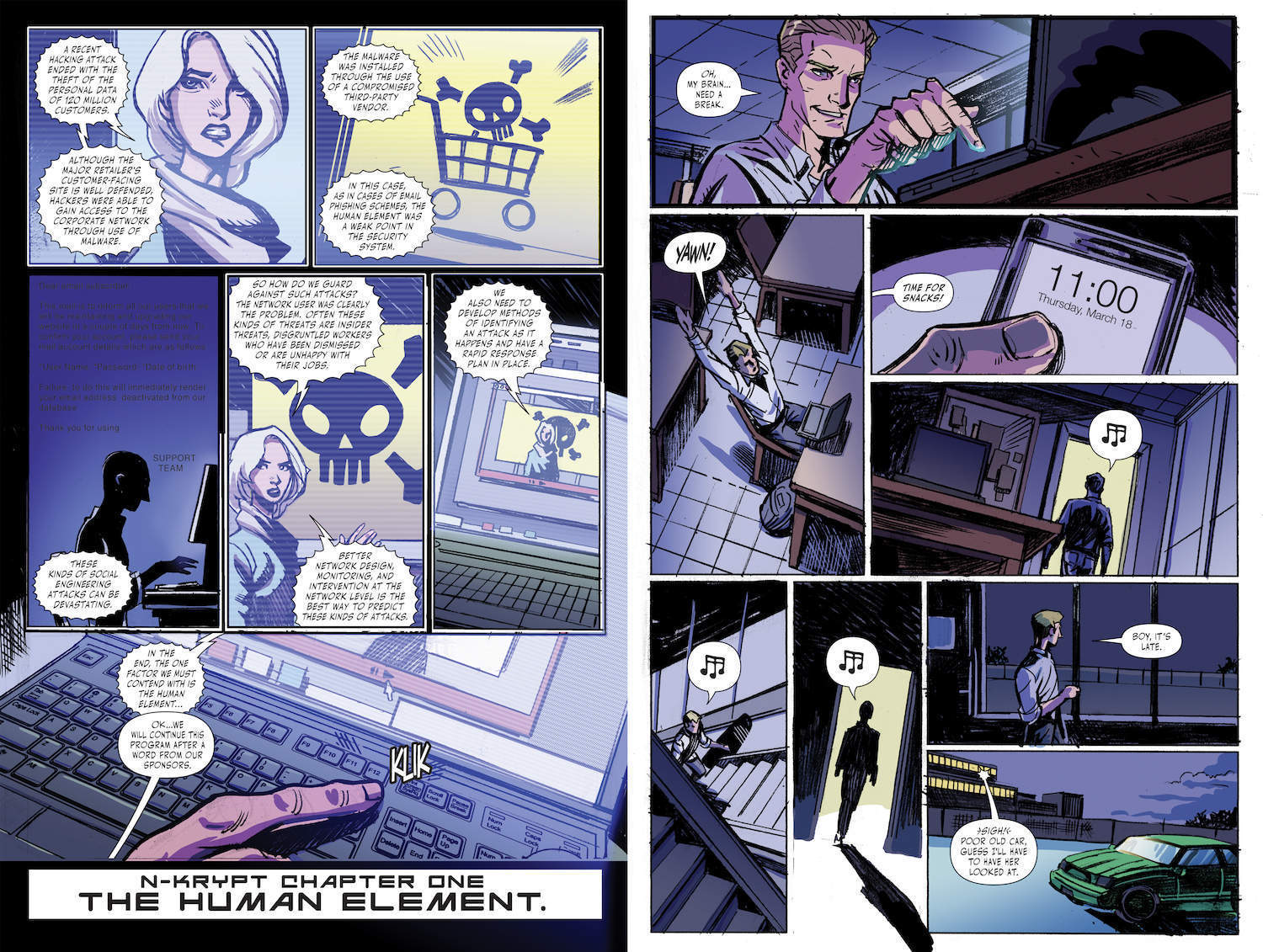
The university’s cyber-security department have created a new comic book called N-Kyrpt: The Human Element to help teach people about cyber-security in a fun, innovative manner.
The plot might not involve superheroes, but the protagonist definitely has to save the day from a dastardly villain:
When a mysterious group invades Ecks Corp, an employee named Sam must single-handedly investigate their hacking attempts. As Sam learns, the greatest—and hardest to prevent—threat to secure networks is the human element. Can Sam execute a rapid response to encrypt Ecks Corp’s data before it’s too late, not only for the Ecks Corp network’s safety but for his own?
You can read the full comic here. It’s actually a tonne of fun and it’ll definitely get readers thinking about how secure their own personal information is online.
Of course, while the comic book is certainly a flashy way of getting the message across, it’s also designed to be informative.
I had a chat to professor Shiu-Kai Chin from Engineering@Syracuse, the online masters degree in cybersecurity from Syracuse University, about the issues behind the comic and why cyber-security is growing more important than ever.
Verdict (V): First question: why did Syracuse University decide to make a comic book out of the issue of the human element?
Professor Chin (C): “This was an idea that came out of our marketing partners who are helping us on the cybersecurity programme. Their people thought it might be a good idea to create a story to show how all this fits together in an entertaining fashion.”
V: The graphic novel is all about ‘the human element’. How would you define this in the simplest terms?
C: “Let’s take something that we’re all familiar with, finance. The financial system’s purpose is to enable commerce by means of worldwide transfers of. If you think about it from that standpoint, not just in terms of bits and bytes and the apps on our phones, human beings play a significant role. These actions must occur if, and only if, they are authenticated and authorised. I want to know who is moving my money around and if something happens to my account it’s fully authorised. And if any action occurs then it was authenticated and authorised.
“If you imagine any machine doing this unsupervised, it doesn’t make sense. Human beings must be deeply integrated into all these systems at all levels. ‘The human element’ is the integration of people into these electronic systems.”
V: Who would you say is most liable to cyber-attacks these days? Is it personal computers or big business?
C: “So, I think the latest ransomware attacks were on hospital records. Any business that relies on electronic data and what amounts to electronic command, control and communication is a potential target. You and I as individuals aren’t a big enough target. Unless someone has a big grudge against us!
“We all rely on financial systems and healthcare systems and so I think the nature of these attacks, particularly the ransomware attacks, exemplify the kinds of attacks the comic highlighted. The comic had somebody getting unauthorised access to destroy something and, the nightmare case, to disrupt or corrupt the data or information.
“So for example, as bad as not being able to get the records in UK hospitals was. Suppose someone changed the data on everybody’s blood type. Imagine would that would do. Nobody would believe the records anymore. Everything would slow down and grind to a halt.
“These are not new ideas but they are new in terms of the global scale because we have chosen to hook up everything to everything else.”
V: Would you say these kind of acts becoming more likely? Or are they getting easier to defend against now that there’s a millennial workforce who are more tech savvy and might be more suspicious of attacks of this nature?
C: “Yes and yes. Kind of contradictory but…
“Because of the internet of things we’ve vastly increased the impact surface – there’s more stuff connected so there’s more stuff to go after. If you can’t get to a system one way there are dozens of other paths you can try. So in that sense it’s more difficult to defend against – there’s more territory to cover.
“The fact that we’re having this conversation and people are concerned about it is actually a very good thing. This is very much like the old shanty towns that preceded all the major cities. In the beginning, people saw value in the location, they erected whatever arbitrary structures they could throw up, it grew, nobody wanted to touch them. But then some sort of disaster would take place and compromise a lot of the town. And this time you rebuild it with standards. So the end of that is the shanty town in cyberspace.”
V: What can companies do to minimize the danger of these attacks?
C: “It should be very much like what the accountants do. Think of information like money, and think of transfer of information like the transfer of funds. Every business accountant has to go through everything. They want to look at the design of the business and the actual controls and checks on who can move money around. Is it properly accounted for and audited?
“You’d see that businesses would ask ‘where are the controls that would stop me from going into an unacceptable loss?’ I mean, I may not have, triple factor authentication on petty cash. But if JP Morgan tried to transfer £200 million in one transaction, you better believe there are all sorts of authentications and authorisations.
“Businesses should think about their information exactly how they think about money. Who has access to it and under what circumstances? The same controls on money should be applied to data at a minimum.”
V: In the comic they show a character who has his password very easily guessed. Is there anything ordinary people can do to improve their passwords?
C: “The number of digits and characters in there can make passwords strong, because the more you have, the more combinations it could be. But then the challenge is how do I make it memorable? The use of mnemonics can help you remember.
“But passwords are probably not always the best technology for authenticating people. Maybe you’ve heard of the three-authentication factors:
- A thing you know – a password.
- Something you have – a physical key or an electronic dongle.
- Something you are – finger prints, voice, or facial recognition.
“My guess is that for really critical things you’ll use some combination of items beyond a password or a pin. For my iTunes account, I’m willing to put less effort into that.
“You cannot protect everything. What are the unacceptable losses? Those are the things you prioritise and take proper precautions to protect.”
V: So in the future we might not use passwords too much?
C: “I don’t think anything will disappear. I think we’ll find, in those three means of authentications. I think institutions will find some combination of those three means of authentication.”
V: How has the teaching of cybersecurity and how to defend against cyber-attacks changed? How often do you have to change the syllabus and teach students new things?
C: “We say the half-life of knowledge in computer engineering is five years. It’s relatively short.
“If you think about what’s on your now – your smartphone. What’s the lifespan of that or any of its apps? It’s probably around six months. But then when it’s a part of computer engineering and computer science, it’s something around five years. But principles of mathematics, logic, physics, design (and that includes security design principles) haven’t really changed at all since mainframe computers.
“So, that stuff is on the order of decades.
“We will teach the principles of mobile applications, just like there are mathematics and design principles of security and those remain pretty stable. In fact, it’s still arguable that mainframe computers are one of the best designs of security still yet to be met by personal computers.
“So the answer is, on the long-lasting stuff we don’t need to revise too often. If I’m deploying an army or technicians, then I may need to keep patching all of my devices and change that pretty often.”
V: Do you think Brexit will make Britain more cyber-secure because we’ll be sharing less data or will we be more susceptible to cyber-attack?
C: “We all share a common base in terms of the integrated circuits, the microprocessors that come out of Intel, and the microprocessors and graphics chips that come out of China.
“Pardon me for saying it this way but if certain factions of the Britain and the United States, isolationist factions, want to drop our global responsibilities, we’ll still be using the technology everybody else does in the medium term.
“Unless they’re willing to make all their own technology and operating systems and see the costs skyrocket, you’ll still all be as vulnerable as ever.”
V: Anything final thoughts to share?
Professor Chin: “You can’t protect everything. Be clear about what the mission is. The ultimate goal since engineering and computer science began is to support society. It’s no different in any of the systems we build. They also have to be trustworthy systems to support society. There’s nothing special about security. It’s part of our responsibilities!”
You can read N-Krypt in its entirety here.







