If you are working from home, you should install the latest Windows update issued by Microsoft as a matter of urgency, as it includes patches to vulnerabilities that hackers are already exploiting in the wild.
Two of the vulnerabilities in question stem from the Adobe Type Manager Library, one of which was first acknowledged by Microsoft in late March.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
At the time the company said that the vulnerability, which can be used as a gateway for severe attacks such as the injection of malware and ransomware on all versions of Windows 10, as well as Windows 7 and Windows Server, was already being used by hackers.
Back then Microsoft was it was “working on a fix”, which it has now completed and is being rolled out to users via the Patch Tuesday update, a monthly security update issued by Microsoft.
However, it is not the only vulnerability being fixed by the latest Patch Tuesday – the latest security update contains a bumper haul of fixes, many of which could enable hackers to cause significant damage to users’ machines if left unpatched.
“This month’s Patch Tuesday is another considerable release, with Microsoft fixing 113 vulnerabilities, 19 of them rated as critical and 94 rated as important. Three of these vulnerabilities were exploited in the wild,” explained Satnam Narang, principal research engineer at Tenable.
With so many people working from home amid the coronavirus, keeping security patches up to date is more vital than ever, as cybercriminals are increasingly targeting businesses that are working remotely.
Vulnerabilities fixed by latest Windows update include SMBGhost
One of the other most significant vulnerabilities that is included in the latest Patch Tuesday update has been given the rare honour of a name: SMBGhost.
This vulnerability is found in a protocol, SMBv3, that is commonly used to connect printers and share files across networks, which may not be an issue for those working purely on their own home laptop, but could be a significant problem for anyone remotely accessing work infrastructure.
It has been a particularly important one for Microsoft to fix as word slipped out about it shortly before the last Patch Tuesday, but the company was not able to prepare a patch in time, meaning hackers could be exploiting it knowing users won’t be able to protect themselves.
While Microsoft did rush out an update in March to fix it, this wasn’t part of a Patch Tuesday release and so will not have been installed by many.
“Proof of Concept (PoC) code that exploits this vulnerability was released on 1 April, but, to this point there has been no confirmation that malware families have incorporated it into their arsenal,” said Allan Liska, senior solutions architect at Recorded Future.
“If you have not patched this vulnerability yet do so immediately.”
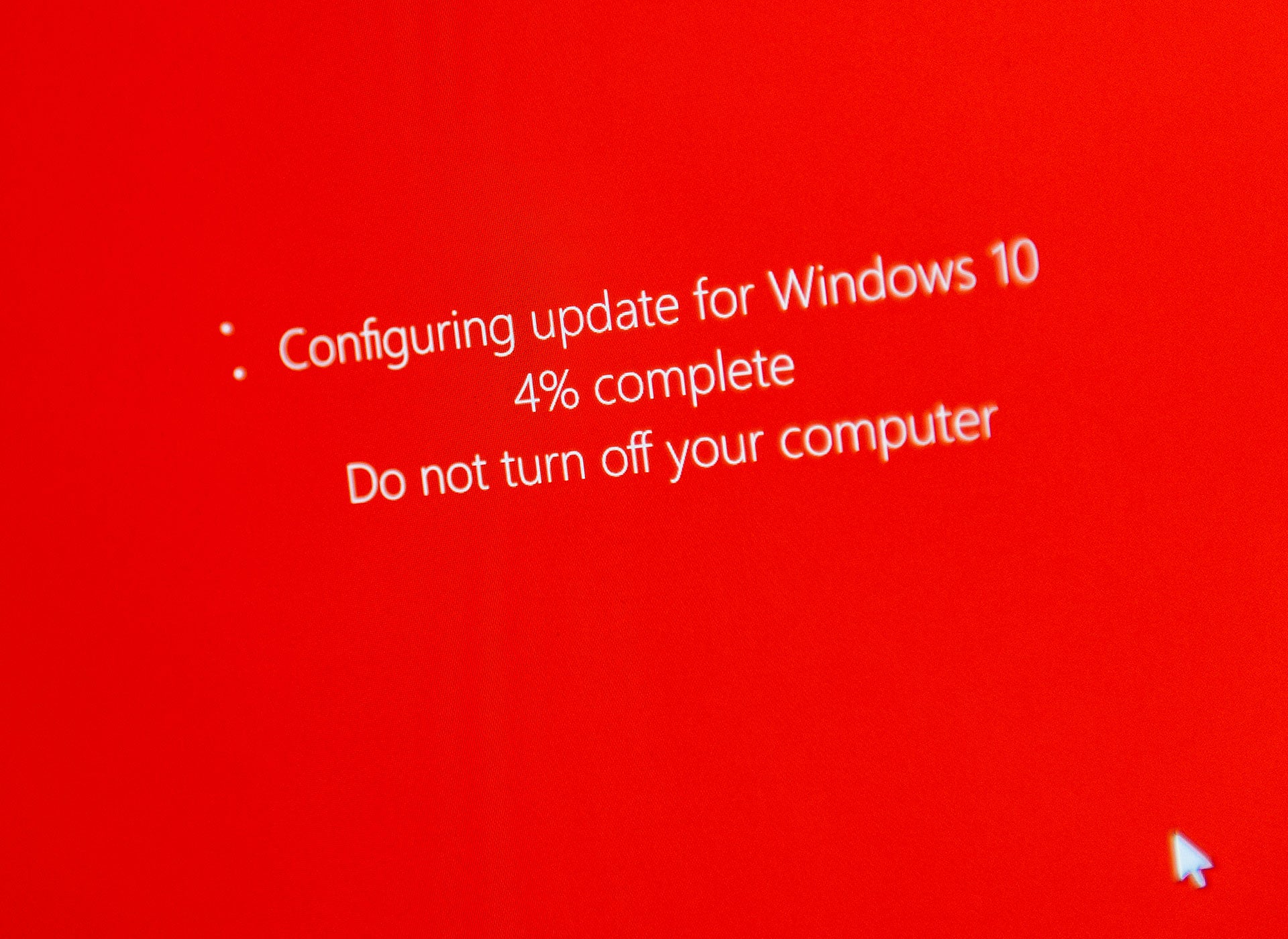
How to update Windows
While the update will be installed automatically for many users, it will not be initiated for those who have opted to manually update, and those that are on low-bandwidth networks may find that it does not initiate immediately.
To check if the update has installed on your Windows 10 machine, go to Settings and select ‘Update & Security’. The Windows Update section will tell you if there are any updates available, and give you the option to install these if they have not already been applied.
Read more: Cyberattackers ramp up efforts against businesses as coronavirus remote working surges