
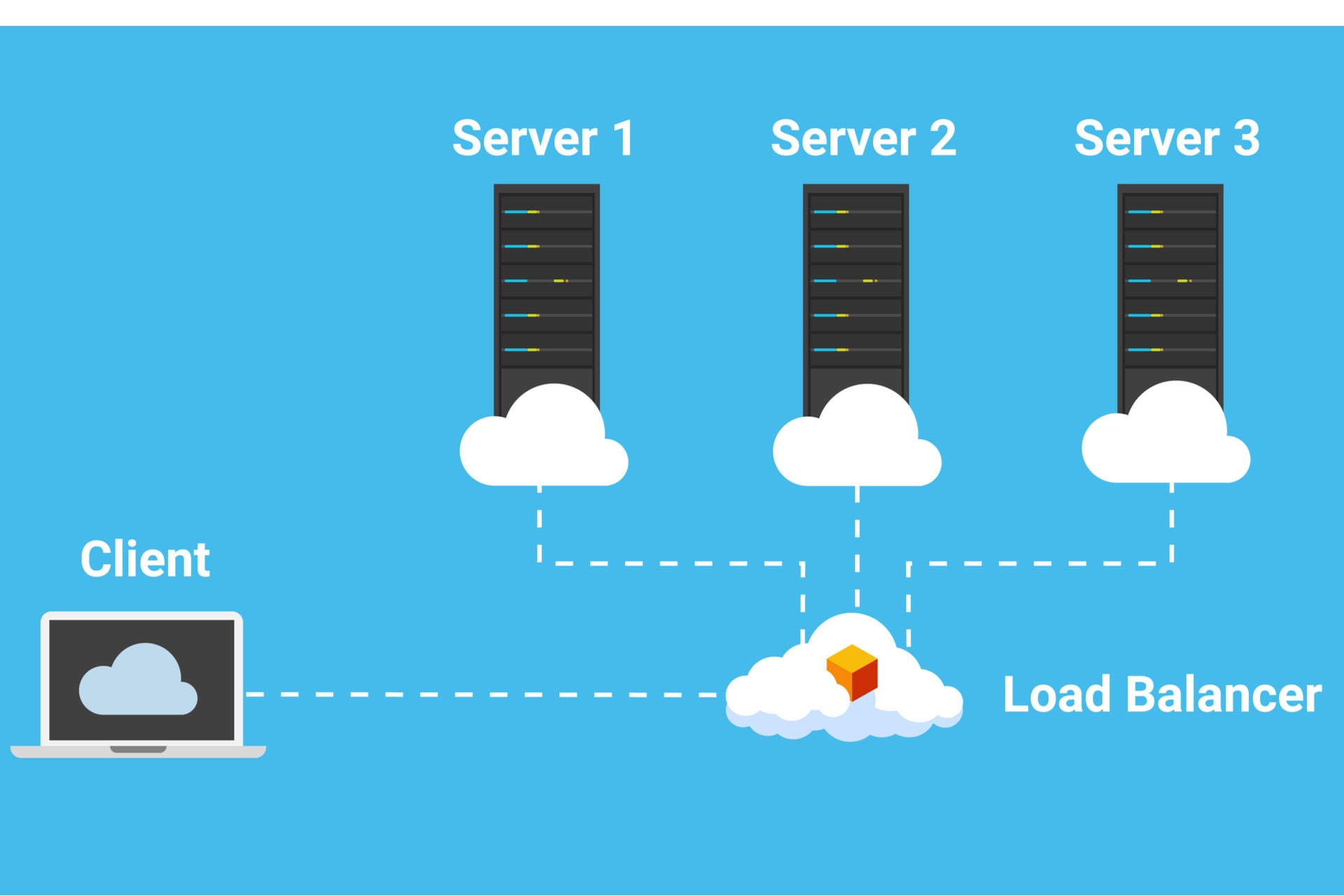
A security researcher has discovered that certain coding practices make it possible for attackers to compromise F5 Networks’ BIG-IP load balancer, a device popular among banks and governments for distributing traffic across devices.
Attackers exploiting this coding practice vulnerability could then carry out a wide variety of cyberattacks against organisations, as well as individuals using the web services of an affected organisation.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
A researcher at Finnish cybersecurity firm F-Secure says he discovered 300,000 BIG-IP load balancer implementations during their investigation, but say the real figure is likely to be far higher. Around 60% were located in the US.
To be clear, the vulnerability is not with F5’s BIG-IP load balancer. The security flaw stems from coding practices related to programming language Tcl. Tcl is used to write the scripts that run BIG-IP’s iRules, which allows BIG-IP to direct incoming web traffic. And if these scripts are written in the wrong way, they create weak points attackers can take advantage of.
F-Secure says attackers could inject arbitrary Tcl commands. Malicious hackers could then use a compromised BIG-IP device to intercept and manipulate web traffic, potentially exposing sensitive information.
They could also use the compromised device to launch further attacks, which could see people using the services of that organisation become the target of a cyberattack.
Load balancer vulnerability is tough to find
“This configuration issue is really quite severe because it’s stealthy enough for an attacker to get in, achieve a wide variety of objectives, and then cover their tracks,” explains F-Secure senior security consultant Christoffer Jerkeby, the researcher who discovered the vulnerability.
“Plus, many organisations aren’t prepared to find or fix issues that are buried deep in software supply chains, which adds up to a potentially big security problem. Unless you know what to look for, it’s tough to foresee this problem occurring, and even harder to deal with in an actual attack.”
Jerkeby revealed his findings to F5 some months ago. Back in May, the US-based firm published more information on the coding flaw here.
In a statement to Verdict, F5 Networks said:
“This is not a vulnerability in Tcl, nor F5 products, but rather an issue relating to coding practices used in creating the scripts. As with most programming or scripting languages, it is possible to write code in a way that creates vulnerabilities.
“We have been working with the researcher on documentation and notification to ensure customers can evaluate their exposure and take necessary steps to mitigate. The best practice for Tcl scripting is to escape all expressions, ensuring they are not substituted or evaluated unexpectedly. Customers are advised to evaluate Tcl scripts and make all changes they deem appropriate under this guidance.”
Customers can find out more information here.
Onus on organisations to fix vulnerability
F-Secure said that in some situations the compromised BIG-IP device would not show any trace of an adversary’s actions, making a response to an attack more challenging and raising the possibility that organisations could be affected without realising.
“Unless an organisation has done an in-depth investigation of this technology, there’s a strong chance they’ve got this problem,” says Jerkeby.
“Even someone incredibly knowledgeable about security that works at a well-resourced company can make this mistake. So, spreading awareness about the issue is really important if we want to help organisations better protect themselves from a potential breach scenario.”
Jerkeby told Verdict that F-Secure is not aware of the vulnerability being used to carry out any real attacks.
“However, this vulnerability is easy to exploit but very hard to detect,” he said. “It is likely that there are hackers out there today who exploit this vulnerability, but the victims never know. Successful attacks reside in memory only, and incoming requests are not logged by default.”
While not everyone using BIG-IP will be affected, F-Secure advises organisations to carry out an audit to check if they are vulnerable to the security flaw. Jerkeby has developed free, open-source tools to identify the BIG-IP security flaw, which is available here and here.
“The upside of this kind of security problem is that not everyone using the product will be affected. But the downside is that the problem can’t be fixed with a patch or software update from the vendor, so it’s up to organizations to do the work to check to see if they have this issue, and fix it if they find it,” explains Jerkeby, who presented his findings at the Black Hat security conference.
“That’s why it’s important for anyone using BIG-IP to be proactive about this.”
Read more: Decade-old vulnerability allows hackers to bug office phones in 90% of Fortune 100







