The technology industry continues to be a hotbed of patent innovation. Activity is driven by the increasing frequency and sophistication of cyber threats, the growing adoption of digital technologies, and the need for robust data protection measures, as well as growing importance of technologies such as secure hash algorithm 2 (SHA-2) and secure hash algorithm 3 (SHA-3), which offer enhanced security features and resistance against cryptographic attacks. These technologies contribute to the development of secure systems, communications, and storage solutions, reinforcing cybersecurity frameworks and fostering digital trust. In the last three years alone, there have been over 1.5 million patents filed and granted in the technology industry, according to GlobalData’s report on Cybersecurity in technology: secure hash algorithms (SHA). Buy the report here.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
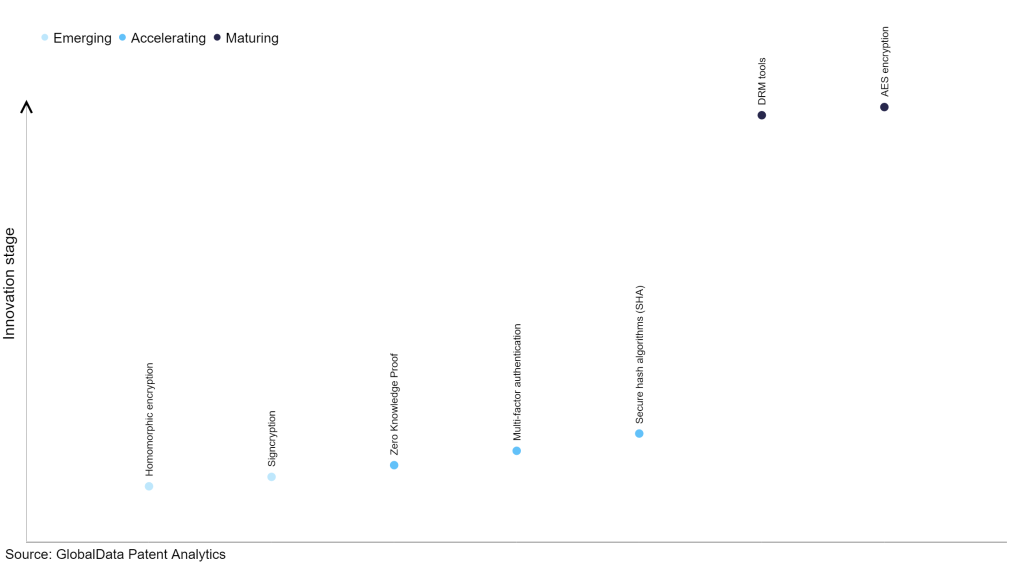
However, not all innovations are equal and nor do they follow a constant upward trend. Instead, their evolution takes the form of an S-shaped curve that reflects their typical lifecycle from early emergence to accelerating adoption, before finally stabilizing and reaching maturity.
Identifying where a particular innovation is on this journey, especially those that are in the emerging and accelerating stages, is essential for understanding their current level of adoption and the likely future trajectory and impact they will have.
185+ innovations will shape the technology industry
According to GlobalData’s Technology Foresights, which plots the S-curve for the technology industry using innovation intensity models built on over 1.6 million patents, there are 185+ innovation areas that will shape the future of the industry.
Within the emerging innovation stage, homomorphic encryption and signcryption, are disruptive technologies that are in the early stages of application and should be tracked closely. Zero knowledge proof, multi-factor authentication and secure hash algorithms (SHA) are some of the accelerating innovation areas, where adoption has been steadily increasing. Among maturing innovation areas are DRM tools and AES encryption, which are now well established in the industry.
Innovation S-curve for cybersecurity in the technology industry
Secure hash algorithms (SHA) is a key innovation area in cybersecurity
Secure hash algorithms (SHA) encompass a collection of cryptographic hash functions formulated by the US National Security Agency (NSA) and released by the National Institute of Standards and Technology (NIST). These algorithms generate a consistent-length message digest derived from input messages of varying lengths, making them well-suited for applications involving digital signatures and data integrity preservation. SHA algorithms are instrumental in ensuring the authenticity and integrity of digital data, establishing robust cryptographic frameworks, and safeguarding sensitive information.
GlobalData’s analysis also uncovers the companies at the forefront of each innovation area and assesses the potential reach and impact of their patenting activity across different applications and geographies. According to GlobalData, there are 600+ companies, spanning technology vendors, established technology companies, and up-and-coming start-ups engaged in the development and application of secure hash algorithms (SHA).
Key players in secure hash algorithms (SHA) – a disruptive innovation in the technology industry
‘Application diversity’ measures the number of applications identified for each patent. It broadly splits companies into either ‘niche’ or ‘diversified’ innovators.
‘Geographic reach’ refers to the number of countries each patent is registered in. It reflects the breadth of geographic application intended, ranging from ‘global’ to ‘local’.
Alibaba Group is the leading patent filer in secure hash algorithms (SHA). The company’s patents are aimed at a data storage method for determining a first check value of a first version of a target object, obtaining a second check value of a second version of the target object, creating a data block comprising the first check value and the second check value, and storing the data block in a blockchain, where the data block stored in the blockchain is immutable.
Other prominent patent filers in the space include nChain and Advanced New Technologies.
By geographic reach, Fortinet leads the pack, followed by Symbolic IO and nChain. In terms of application diversity, Alibaba Group holds the top position, followed by Advanced New Technologies and nChain.
Cybersecurity innovation in secure hash algorithms (SHA) can play a critical role in safeguarding sensitive data and enhancing digital security. Secure hash algorithms provide a vital cryptographic function by transforming data into a fixed-size hash value, ensuring data integrity and authenticity.
To further understand how cybersecurity is disrupting the technology industry, access GlobalData’s latest thematic research report on Cybersecurity.
Data Insights
From

The gold standard of business intelligence.
Blending expert knowledge with cutting-edge technology, GlobalData’s unrivalled proprietary data will enable you to decode what’s happening in your market. You can make better informed decisions and gain a future-proof advantage over your competitors.






