Guess what – it’s a myth that Apple’s Mac operating system is any less vulnerable to exploit than Microsoft’s Windows. And if you’re a user of Apple’s iOS mobile operating system, you’re also at risk of falling victim to malicious actors according to research by Google’s Threat Analysis Group (TAG).
TAG has discovered a small number of hacked websites being used to exploit as many as five iOS vulnerability to compromise iPhone devices, with at least one of these being a previously undiscovered zero-day vulnerability.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
Malicious actors aimed to carry out indiscriminate watering hole attacks by infecting websites that particular groups of users – in this case iOS users – are likely to visit.
Rather than websites set up to trick victims, they appear to be legitimate websites that have been compromised.
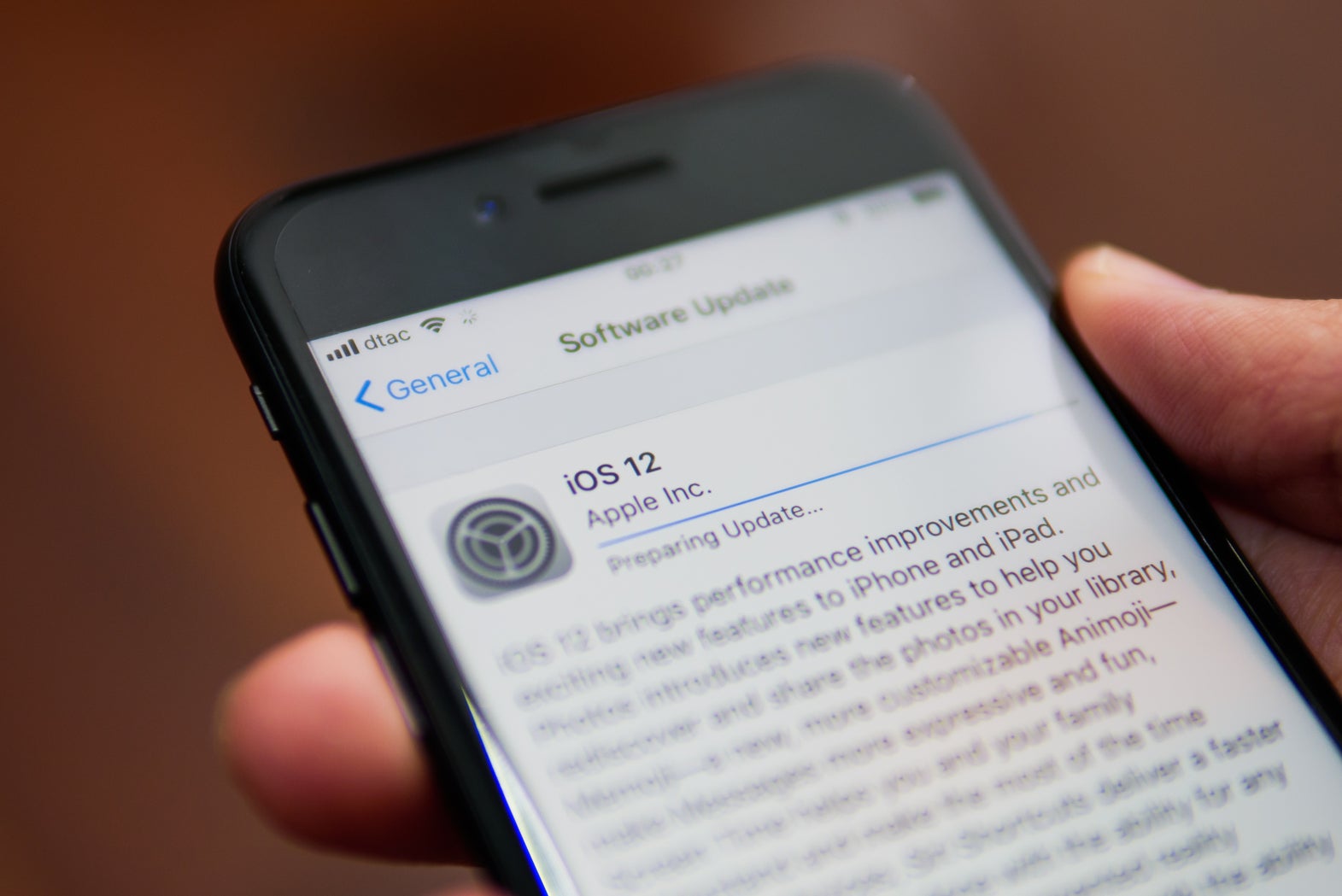
Google researchers believe the first of these compromised sites began distributing malware in 2016, starting with exploits for iOS 10. The latest exploit chain targeted the latest version of Apple’s operating system, iOS 12. However, this has since been patched by Apple.
The researchers estimate that thousands of visitors access the discovered sites each week, and the malicious actors do not require a visitor to download a file for the attack to be carried out.
If the attack is successful, the website installs a monitoring malware on the compromised device.
The malware writes itself to the device’s /tmp folder, but is unable to permanently write itself to the infected device. This means that rebooting the device will remove the infection.
However, until this occurs, the implant will communicate with the attacker’s command-and-control server every 60 seconds, which provides instructions on what information to steal from the device.
The attackers are able to take photographs, email data, contact lists and GPS location data from the device. Likewise, it is also able access the database files of encrypted messaging apps such as Whatsapp and Telegram, allowing the attacker to see message contents in plain-text.
A wake up call for iOS users
“I hope that this will be a wake-up call for anyone that has been under the impression that iOS phones are invulnerable to malware exploiting system and application vulnerabilities,” Boris Cipot, a senior sales engineer at Synopsys, said.
“For a long time, there was a myth that iOS and OSX are secure operating systems and don’t need any security systems like anti-malware to protect them. This last attack example just shows that there is no such thing as a completely secure operating system.”
According to Statista, 73.8% of malware attacks are launched against Windows users, with another 5.6% of attacks launched against Google’s Android users. Other operating systems make up just 20.6% of malware attacks.
However, Apple’s reputation for building secure products could see it targeted by cybercriminals looking to boost their reputation.
“Not only would such inconvenience or even malware have such a damaging effect to Apple and its users, cybercriminals around the world see breaking Apple’s ecosystem as a sort of a pinnacle of their ‘career’ so this amount of attacking will only ever increase,” Jake Moore, a cybersecurity specialist for ESET, said. “There are much kudos to be had to take down such a secure environment of this level that it gets more attention than it possibly warrants from bad actors.”
Given the level of complexity in software development today, catching all vulnerabilities before new software is launched proves difficult. However, companies will commonly release patches after exploits are discovered in order to minimise opportunities for exploitation. Discovering like this highlight the importance of keeping devices up to date, to ensure that these patches have been applied.
“This just highlights how important it is to keep your devices updated to the latest iOS,” Moore said. “Threat actors will not stop at anything to try and exploit Apple’s operating system where they can.”
Read more: Ransomware resurgence as number of new strains grows 118%







