
A new phishing campaign is mimicking the UK Ministry of Justice in order to scare victims into installing information-stealing malware.
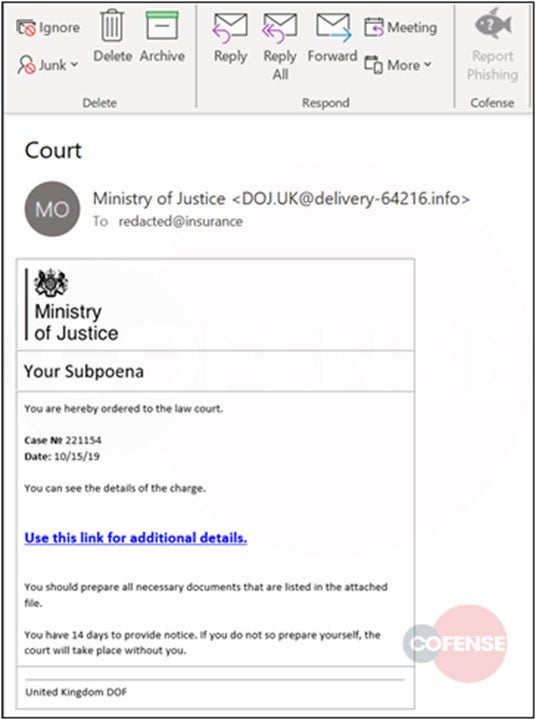
Identified by Cofense Intelligence, the campaign involves sending would-be victims an email that appears to be from the Ministry of Justice.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
Entitled “Your Subpoena”, it tells the recipient that they have been “ordered to the law court”, prompting them to click on a link to “see the details of the charge”.
However, this link instead initiates a chain of redirections that ultimately lead to a Microsoft World file that contains a malicious macro. When executed, this downloads a common information-stealing malware known as Predator the Thief.
First observed in July 2018, this publicly available malware is able to steal passwords stored in web browsers, take pictures using the infected computer’s webcam and collect data from files and programs.
The email also includes a warning that the recipient has 14 days to comply with the subpoena notice, which Cofense characterises as “a scare tactic designed to panic users into clicking”.
Ministry of Justice phishing campaign designed to con software and users alike
The campaign, which Cofense Intelligence has already identified as having been sent to employees at insurance and retail companies, is designed not only to fool users, but to bypass many security systems to maximise its chances of success.
The initial link the email contains is to a Google Docs page that is completely benign in and of itself, but which the initiates the chain of redirects that ultimately lead to the infected file.
As Google Docs is a trusted source, this enables the Ministry of Justice-themed phishing email to appear legitimate to many email security stacks, including the widely used Secure Email Gateway (SEG) from FireEye, meaning it will end up in many enterprise inboxes.
Cofense has been keen to point out that its own solution does catch such approaches, which is why it was able to identify the campaign.
Aside from having an appropriately robust email security stack, organisations are advised to disable Microsoft macros by default. For users, this is another case of exercising significant caution.
Read more: How to spot spear phishing and protect your business from costly attacks







