Security researchers have uncovered a 5G network slicing security flaw that could leave enterprises using the technology exposed to data theft or denial-of-service attacks.
According to a report published by mobile network security firm AdaptiveMobile Security, the vulnerabilities affect hybrid setups where both 5G and older generations of network technologies are used.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
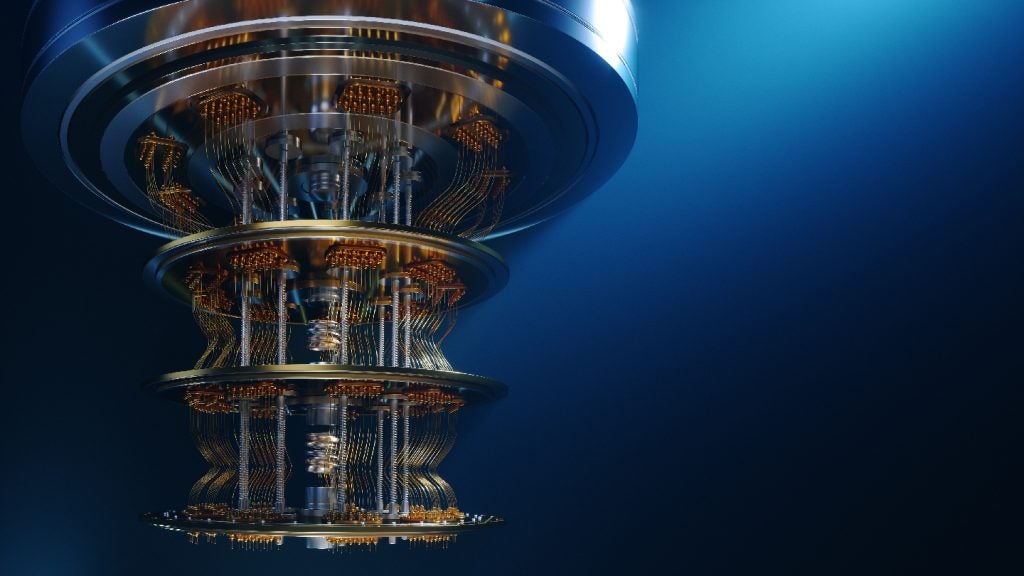
Network slicing is a type of architecture that can divide a 5G network into multiple virtual sub-networks that share the same physical infrastructure. These distinct virtual segments can provide varying speeds and resources to respond to different traffic demands, and might be used by different organisations depending on their needs.
The concept is touted as one of the key benefits associated with 5G. For example, a mobile operator could use slicing to offer different capabilities to different customers. Online gaming systems and driverless car networks could be offered very low latency, for instance: or emergency services could be given dedicated access that couldn’t be swamped by ordinary phone users in crisis-hit areas.
In a 36-page report, AdaptiveMobile said the attacks are possible because of “a lack of mapping between the application and transport layers identities”. This industry-standard flaw means that an attacker gaining access to a mobile operator’s 5G service-based architecture would have access to both the operator’s core network and the network slices dedicated to other enterprises.
AdaptiveMobile gives the example of a malicious hacker compromising telecom equipment at the edge of the network and then using the slicing flaw to move across other virtual networks. This could “risk the loss of sensitive location data”, the security firm said. Such data could include user location tracking and information for billing customers. Alternatively, the attacker could shut down the network in a denial-of-service attack.
The risk of threat actors taking advantage of this vulnerability is currently relatively low due to the limited amount of network slicing currently in use across existing 5G networks, AdaptiveMobile said.
The security firm has shared its research with global mobile industry trade body the GSMA, along with other operators and standards bodies.
“5G is driving the mobile industry into adopting the technology and techniques of the IT world to increase efficiency and improve functionality. However, while this is laudable, there needs to be a wider mindset change,” said Silke Holtmanns, head of 5G security research at AdaptiveMobile Security.
“When it comes to securing 5G, the telecoms industry needs to embrace a holistic and collaborative approach to secure networks across standards bodies, working groups, operators and vendors.”
She added: “Using IT for telco is a steep learning curve for all.”