
The cyberwar in Ukraine intensified over the weekend as hacking group Anonymous joined the fray, declaring that it is officially at war “against the Russian government”. The group has already taken credit for a number of cyber incidents, including distributed denial of service (DDoS) attacks against Russian government platforms and broadcasters. However, the hacking war worsening also raises the risk of businesses in other countries being caught in the digital blast zone.
“With cyberwars, businesses away from the war zone inevitably get caught up in the online crossfire from the intensifying phishing and DDoS attacks,” Jake Moore, global cybersecurity advisor at digital defence firm ESET, tells Verdict.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
Hacking groups usually like keeping to the shadows, but Anonymous instead made its intent to join the war effort very public on February 24 by posting it on a Twitter account, @YourAnonOne, which has been linked to the group.
“The Anonymous collective is officially in cyberwar against the Russian government,” the tweet said.
Anonymous claims to have stayed busy since. The organisation has taken credit for DDoS attacks which have downed Russian government sites and at times taken Kremlin mouthpiece Russia Today off the web.
Anonymous also said it had hacked the Russian Ministry of Defence database. On Sunday the group claimed to have hacked Russian state TV channels, posting pro-Ukraine content including patriotic songs and images from the invasion. These attacks coincided with thousands of Russian taking to the streets to join anti-war protests over the weekend.
It is difficult, however, to attribute these attacks to Anonymous with absolute certainty. The informal nature of the group means tracking its activities is challenging, especially given that the Russian state is highly unlikely to share the data about the attacks with outsiders.
Russia Today did, nonetheless, openly blame its site downage on Anonymous, saying the attacks came from “some 100 million devices, mostly based in the US.”
While it is difficult to confirm the details of Anonymous’ involvement, Moore notes that the narrative fits in with the group’s history.
“Anonymous are renowned for conducting this sort of activity and often act as a nation state of their own with their capabilities and power,” Moore says. “It is clear that Ukraine will require cyber support. With Anonymous heavily involved, it will be much more difficult to attribute cyber attacks on Russia to any particular country. This will help to avoid further physical attacks.”
Anonymous has previously targeted the CIA, the Church of Scientology, Islamic State and various organisations which it has deemed to be enemies of Wikileaks founder Julian Assange. Following a period of reduced activity following a number of arrests in the early 2010s, the hacktivist collective reemerged after the murder of George Floyd. The group claimed responsibility for hacking the Minneapolis police department and turning the website of a minor United Nations agency into an online memorial of Floyd.
The news of Anonymous taking credit for hacks against Russia comes after the Ukraine government reportedly attempted to enlist its own underground hacking community in the war effort, having had a cybersecurity firm post ads for people to sign up. It is unclear if Anonymous’ activities are linked to this outreach.
On February 26, Ukraine’s deputy prime minister and the minister for digital transformation, Mykhailo Fedorov, announced the creation of a volunteer cyber army, Wired reported.
“We have a lot of talented Ukrainians in the digital sphere: developers, cyber specialists, designers, copywriters, marketers,” he said in a post on his official Telegram channel. “We continue to fight on the cyber front.”
Some ingenious Ukrainian women have apparently mounted a different kind of cyber campaign by matching with Russian soldiers who are now showing up on the dating app Tinder, reportedly luring them into giving away their positions. The app only shows singles within a certain radius from the user.
Ukraine cyberwar underway
Anonymous declaring cyberwar on Russia comes after Vladimir Putin’s regime has been accused of launching smaller attacks against governmental agencies and other organisations in Ukraine.
However, these attacks do not differ vastly from the ongoing digital siege Russia has waged against Ukraine since it invaded the Crimean peninsula in 2014. There have been reports about new strains of malware being deployed by Sandworm, a Russian state-linked hacking group, and other groups. So far, though, these attacks have seemingly been limited to a few hundred infected computers, according to analyst estimates.
Nonetheless, cybersecurity experts warn that once a computer virus is lose in the world, then it could spread just as easily as biological contagions like Covid-19 do. They have a point. In 2017, Sandworm launched the NotPetya attack in Ukraine, but the malware quickly spread out of control, crippling ports, government platforms and companies around the world, including in Russia.
“The war we see on TV is only a fraction of the conflict,” Hitesh Sheth CEO of Vectra AI, tells Verdict. “Cyber weapons are doing at least equal damage to Ukrainian computer networks, particularly financial and military systems. We will never have more vivid proof that offensive cyber action is now a first-strike tactic, on a par with kinetic warfare.
“The sobering difference: conventional war is waged between nation states. Cyber war poses severe risk to private interests, however reluctant and unwilling they are to become combatants. Escalating cyber conflict can lead to unanticipated consequences and casualties. Nobody is assured of remaining a mere spectator.
“To that end, no public or private organisation can afford complacency about the events we are watching in real time. They prove the alarming point that antiquated cyber defences centered on perimeter protection will fail under fire. Security begins at home, and private interests cannot rely on state-sponsored protection. They must audit and reinforce cyber defenses and prioritise AI-augmented detection and response. Doing so will contribute to stability in a worrisome time.”
Good news for cybersecurity firms
Cybersecurity experts have reason to be publicly alarmist: the higher the fear of cyberattacks, the bigger the demand for their services. Tellingly, publicly traded cybersecurity companies like Telos, Palo Alto Networks and CrowdStrike saw their shares spike in late February as the Russian invasion of Ukraine begun. At the same time the stock market slumped and cryptocurrencies‘ value plummeted, casting doubt over bitcoin’s reputation as a safe haven asset like gold.
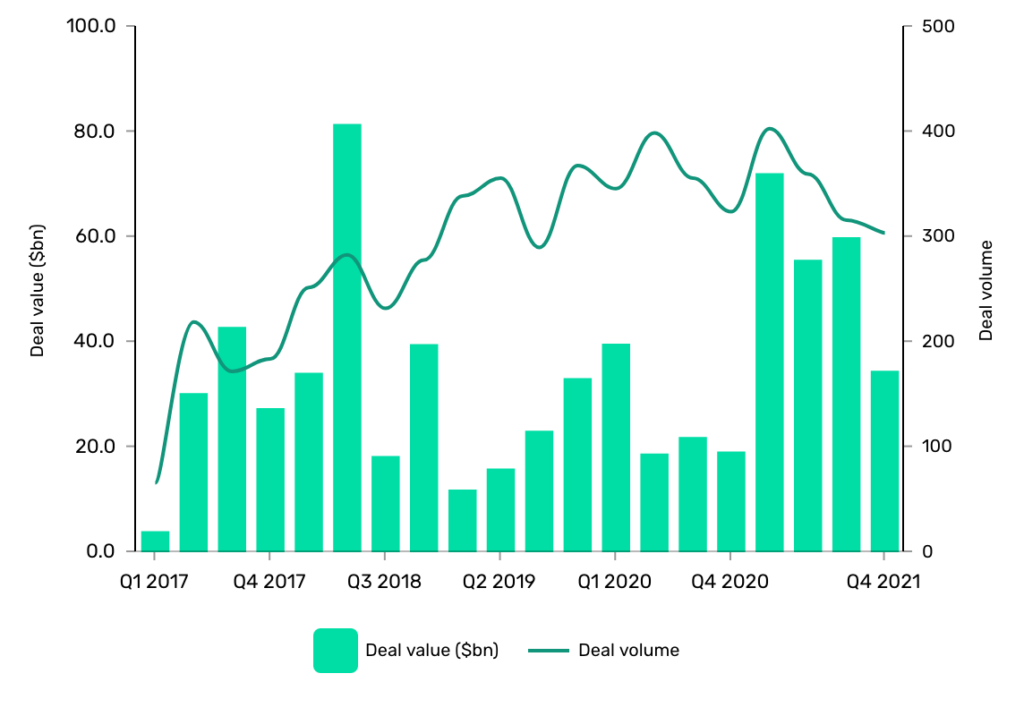
Similar spikes were seen in investment deals during the pandemic when Covid-19 created more opportunities for ransomware gangs to attack companies via their socially distanced employees. A bigger threat forced more companies to strengthen their cybersecurity, which meant more investment.
Back in 2017, GlobalData recorded 641 deals worth $103.29bn in total. Fast forward to 2021 and the number of deals had jumped to 1,383 deals worth $220.93bn in total.
The surge in cybersecurity stocks last week suggests that similar mechanisms are at work now, meaning that the business community expects more hacks to come.
GlobalData is the parent company of Verdict and its sister publications.







