First they came for Elon Musk, then they came for Bill Gates. Jeff Bezos, Kanye West, Joe Biden and countless others were next and in less than two hours it became clear that Twitter was facing the biggest security threat in its history.
The Twitter hack, which started Wednesday around 8pm UK time, saw scammers seemingly gain access to all 350 million Twitter accounts and hijack verified accounts to promote a Bitcoin scam.

Access deeper industry intelligence
Experience unmatched clarity with a single platform that combines unique data, AI, and human expertise.
First the scammers took over the accounts of cryptocurrency organisations, such as Gemini and Binance.
Then, one by one, the accounts of some of the most recognisable names in the world, including former US president Barack Obama, posted a message asking people to transfer $1,000 worth of the digital cryptocurrency to a Bitcoin wallet. In return, the scammers promised to send $2,000 back.
“This was the biggest security breach in Twitter’s history, but ordinary users were not affected by it at all – unless they fell for the scams posted by the hacked celebrities,” says Mikko Hyppönen, chief research officer at F-Secure.
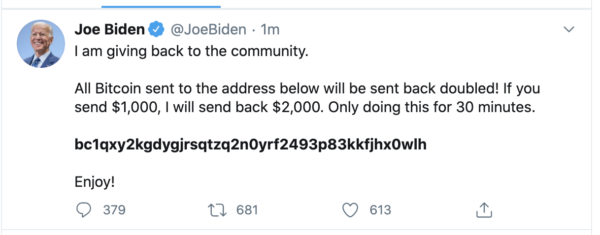
In total, more than $110,000 was transferred to the hacker’s Bitcoin wallet – although it is possible they transferred some of this money themselves to give the impression that more were falling for the scam.
Meanwhile, Twitter scrambled to get a hold on the situation and eventually decided to take the nuclear option of temporarily blocking every verified user from tweeting.
How was Twitter hacked?
Twitter is yet to explain in detail how the hack took place, but it appears those behind it were able to gain administrative privileges.
In a statement, the firm said: “We detected what we believe to be a co-ordinated social-engineering attack by people who successfully targeted some of our employees with access to internal systems and tools.”
According to Vice, sources with knowledge of the hack said a “Twitter insider” was paid by the scammers to carry out the account takeovers.
Another source, speaking to TechCrunch, backed up claims that a Twitter admin tool was used to carry out the hack but diverted from Vice’s sources by suggesting a Twitter employee’s corporate account was hijacked.
Twitter said it is still investigating whether an employee was hacked or granted access to the scammers.
Insider threat is a security risk that can render the most robust defences useless.
“Technical countermeasures against phishing attempts and detecting malicious activities today are much more robust than they have been in the past,” says Stuart Reed, UK director at Orange Cyberdefense.
“The human, on the other hand, is more complex and harder to predict in certain scenarios while easy to manipulate in others.”
But questions remain about why some Twitter employees had such high-level access – and why more safeguards weren’t in place to prevent such an attack from happening.
The theories – and why some don’t hold water
Given the admin level access the Twitter hacker seemed to have, many have wondered why they opted for a low-level cryptocurrency scam.
Why not send some market-moving tweets from high-profile accounts and watch the money come in as the share price rises or falls?
Well, doing so would require far more planning, capital and risk. Investing would leave a paper trail for the authorities, and to make significant profits the scammers would need to have large cash reserves.
“For someone with no resources, winning big on the stock market is almost impossible even if the game is rigged,” says Forbes cryptocurrency journalist and former Verdict editor Billy Bambrough.
He points to the 11% rise in Tesla’s share price following Musk’s now-infamous “funding secured” tweet about taking Tesla private.
“You need deep pockets and a lot more planning to make even $100,000 off a short-term market move of 11%.”
But if hackers had ‘god-level’ access, why not read the private messages of the rich and powerful to gather dirt for extortion?
It remains possible that the hackers did this as well. However, there’s no guarantee that the scammers would uncover blackmailable material from the high-profile accounts, nor is it certain that they would have paid for silence – making it a far riskier gambit.
But there is also nothing as of yet to suggest that the Twitter hackers even had access to direct messages.
James Linton, a cybersecurity expert who formerly used social engineering techniques to carry out a string of pranks against celebrities and politicians, has his doubts.
“I doubt that [admin] panel would have access to DMs, that’s a bad thing to give out at all – let alone to multiple people,” he tells Verdict. “Gmail can’t even look at the emails of an account they suspect is committing crime.”
Twitter hack: Was a nation state involved?
There is nothing yet to suggest that nation-state hackers were involved in the Twitter scam, but that hasn’t stopped people from wondering why the access wasn’t sold on for that purpose.
Marcus Hutchins, the security researcher who temporarily halted the WannaCry ransomware attack, has a simpler explanation.
“Sometimes hackers come across valuable access they don’t know how to properly monetise,” he wrote on Twitter. “Just because they only made $100k from having access to almost every Twitter account doesn’t necessarily mean there’s a deeper hidden motive. Some hackers just aren’t creative.”
Some have speculated that the Bitcoin scam was cover for a larger, more sinister attack. As of yet, there is no evidence of this or any indication to what that might entail.
While there may one day be evidence that supports these theories, for now it seems best to assume Occam’s Razor – that the hacker wanted a quick way to make some cash that is difficult to trace.
“They could have done potentially far more damage,” says Liviu Arsene, global cybersecurity researcher at Bitdefender.
“Instead, by delivering a simple Bitcoin scam, we could be looking at attackers that wanted to quickly monetise their access, instead of a highly coordinated and sophisticated operation performed by an advanced persistent threat group.”
What it means for Twitter
The hack raises serious concerns about the safeguards that Twitter has in place to protect its administrator accounts.
“Employees who have access to systems or tools that could abuse Twitter accounts should have strong security controls such as Multi-Factor Authentication, Access Workflows, Sessions Recording, Automated Rotation of privileged accounts passwords and additional authorisation controls,” says Joe Carson, chief security scientist at Thycotic.
The hack is particularly damaging ahead of the US presidential election in November. Notably, Trump was not targeted by the Twitter hacker – causing some to speculate that the attack was politically motivated. But Twitter CEO Jack Dorsey now needs to provide reassurance that his company is equipped to fend off political interference, especially following previous misinformation campaigns on the platform.
It also puts pressure on Dorsey, who has previously come under fire for splitting his time running the Twitter alongside payments firm Square.
“This attack is a stark reminder of just how fragile platform security can be, and that despite our best efforts at locking accounts down individually, it’s all for nothing if things go wrong behind the scenes,” says Chris Boyd, lead malware intelligence analyst at Malwarebytes.
“Given how much Twitter drives conversation generally, we should probably be thankful the hackers were more interested in making easy Bitcoin cash than looking to cause chaos on a social, political, or economic scale. The consequences of a rogue, compromised Trump tweet (for example) could be devastating.”







